HDU
来源:互联网 发布:java简历 编辑:程序博客网 时间:2024/06/06 00:39
点击打开题目链接
Isabella's Message
Time Limit: 2000/1000 MS (Java/Others) Memory Limit: 32768/32768 K (Java/Others)Total Submission(s): 2579 Accepted Submission(s): 762
Problem Description
Isabella and Steve are very good friends, and they often write letters to each other. They exchange funny experiences, talk about people around, share their feelings and write about almost everything through the letters. When the letters are delivered, they are quite afraid that some other people(maybe their parents) would peek. So they encrypted the letter, and only they know how to decrypt it. This guarantees their privacy.
The encrypted message is an N * N matrix, and each grid contains a character.
Steve uses a special mask to work as a key. The mask is N * N(where N is an even number) matrix with N*N/4 holes of size 1 * 1 on it.
The decrypt process consist of the following steps:
1. Put the mask on the encrypted message matrix
2. Write down the characters you can see through the holes, from top to down, then from left to right.
3. Rotate the mask by 90 degrees clockwise.
4. Go to step 2, unless you have wrote down all the N*N characters in the message matrix.
5. Erase all the redundant white spaces in the message.
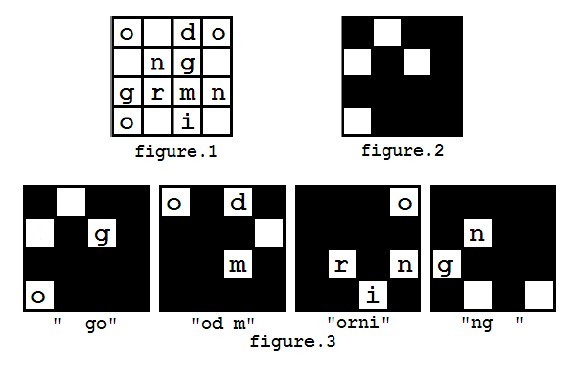
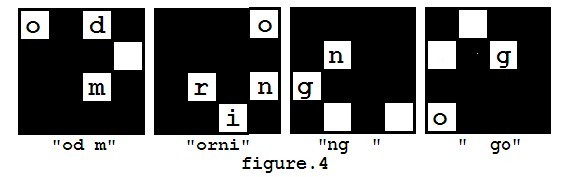
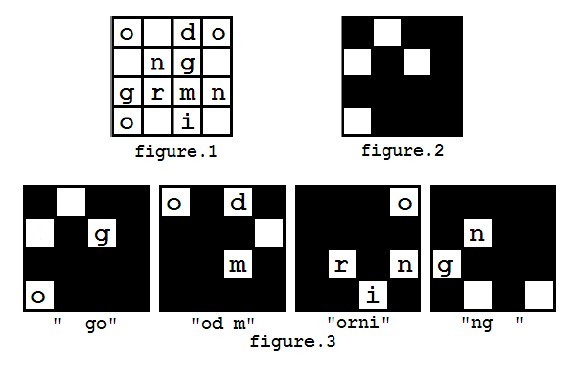
For example, you got a message shown in figure 1, and you have a mask looks like figure 2. The decryption process is shown in figure 3, and finally you may get a message "good morning".
You can assume that the mask is always carefully chosen that each character in the encrypted message will appear exactly once during decryption.
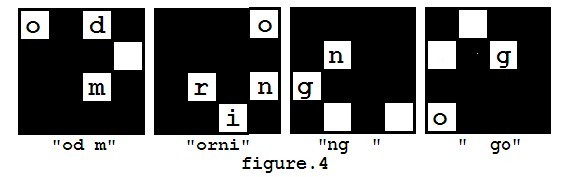
However, in the first step of decryption, there are several ways to put the mask on the message matrix, because the mask can be rotated (but not flipped). So you may get different results such as "od morning go" (as showed in figure 4), and you may also get other messages like "orning good m", "ng good morni".
Steve didn't know which direction of the mask should be chosen at the beginning, but after he tried all possibilities, he found that the message "good morning" is the only one he wanted because he couldn't recognize some words in the other messages. So he will always consider the message he can understand the correct one. Whether he can understand a message depends whether he knows all the words in the message. If there are more than one ways to decrypt the message into an understandable one, he will choose the lexicographically smallest one. The way to compare two messages is to compare the words of two messages one by one, and the first pair of different words in the two messages will determine the lexicographic order of them.
Isabella sends letters to Steve almost every day. As decrypting Isabella's message takes a lot of time, and Steve can wait no longer to know the content of the message, he asked you for help. Now you are given the message he received, the mask, and the list of words he already knew, can you write a program to help him decrypt it?
The encrypted message is an N * N matrix, and each grid contains a character.
Steve uses a special mask to work as a key. The mask is N * N(where N is an even number) matrix with N*N/4 holes of size 1 * 1 on it.
The decrypt process consist of the following steps:
1. Put the mask on the encrypted message matrix
2. Write down the characters you can see through the holes, from top to down, then from left to right.
3. Rotate the mask by 90 degrees clockwise.
4. Go to step 2, unless you have wrote down all the N*N characters in the message matrix.
5. Erase all the redundant white spaces in the message.
For example, you got a message shown in figure 1, and you have a mask looks like figure 2. The decryption process is shown in figure 3, and finally you may get a message "good morning".
You can assume that the mask is always carefully chosen that each character in the encrypted message will appear exactly once during decryption.
However, in the first step of decryption, there are several ways to put the mask on the message matrix, because the mask can be rotated (but not flipped). So you may get different results such as "od morning go" (as showed in figure 4), and you may also get other messages like "orning good m", "ng good morni".
Steve didn't know which direction of the mask should be chosen at the beginning, but after he tried all possibilities, he found that the message "good morning" is the only one he wanted because he couldn't recognize some words in the other messages. So he will always consider the message he can understand the correct one. Whether he can understand a message depends whether he knows all the words in the message. If there are more than one ways to decrypt the message into an understandable one, he will choose the lexicographically smallest one. The way to compare two messages is to compare the words of two messages one by one, and the first pair of different words in the two messages will determine the lexicographic order of them.
Isabella sends letters to Steve almost every day. As decrypting Isabella's message takes a lot of time, and Steve can wait no longer to know the content of the message, he asked you for help. Now you are given the message he received, the mask, and the list of words he already knew, can you write a program to help him decrypt it?
Input
The first line contains an integer T(1 <= T <= 100), indicating the number of test cases.
Each test case contains several lines.
The first line contains an even integer N(2 <= N <= 50), indicating the size of the matrix.
The following N lines each contains exactly N characters, reresenting the message matrix. The message only contains lowercase letters and periods('.'), where periods represent the white spaces.
You can assume the matrix contains at least one letter.
The followingN lines each containsN characters, representing the mask matrix. The asterisk('*') represents a hole, and period('.') otherwise. The next line contains an integer M(1 <= M <= 100), the number of words he knew.
Then the following M lines each contains a string represents a word. The words only contain lowercase letters, and its length will not exceed 20.
Each test case contains several lines.
The first line contains an even integer N(2 <= N <= 50), indicating the size of the matrix.
The following N lines each contains exactly N characters, reresenting the message matrix. The message only contains lowercase letters and periods('.'), where periods represent the white spaces.
You can assume the matrix contains at least one letter.
The followingN lines each containsN characters, representing the mask matrix. The asterisk('*') represents a hole, and period('.') otherwise. The next line contains an integer M(1 <= M <= 100), the number of words he knew.
Then the following M lines each contains a string represents a word. The words only contain lowercase letters, and its length will not exceed 20.
Output
For each test case in the input, print one line: "Case #X: Y", where X is the test case number (starting with 1) and Y is Isabella's message.
If Steve cannot understand the message, just print the Y as "FAIL TO DECRYPT".
If Steve cannot understand the message, just print the Y as "FAIL TO DECRYPT".
Sample Input
34o.do.ng.grmno.i..*..*.*.....*...2goodmorning4..lfeoyvoeouvrer..*..*......*.*.5iyoutheloveforever4.sles.c.e.fs..uu*....*.....*..*.1successful
Sample Output
Case #1: good morningCase #2: love you foreverCase #3: FAIL TO DECRYPT
Source
2011 Asia ChengDu Regional Contest
Recommend
chenyongfu | We have carefully selected several similar problems for you: 4118 4112 4114 4115 4111
题目大意:
给出一个n*n的格子,格子里面有字母和空格,然后给出一个n*n的挡板,*处透明。然后给出多个字符串,问板子经过3个90°后形成的4个字母组合能否组成所给出的字符串(多种输出字典序最小)。
思路:
字符串模拟,WA了n!次,怀疑人生。
首先整理一下各种输入在输入字符串时候的情况:
scanf:遇到空格,TAB,回车键停止 不舍弃最后回车符(将回车留在缓冲区)
gets:遇到回车键停止 舍弃最后回车符
cin:遇到空格,TAB,回车键停止 不舍弃最后回车符(将回车留在缓冲区)
getline: 遇到回车键停止舍弃最后回车符
所以当使用scanf或cin读入一个字符串后,如果不进行清缓冲区操作,下次读入时则直接从缓冲区读数据,一般可用getchar()吃掉最后回车。
具体区别可以参考scanf()、getchar()、gets()、cin之间的区别
然后旋转3次,四种组合,用map存字典,开始匹配即可。注意对空格的处理和初始化即可。
附上AC代码:
#include<iostream>#include<cstring>#include<string>#include<algorithm>#include<cstdio>#include<map>#include<vector>using namespace std;map<string,int>word;char s[55][55];string str[4];string ans[4];int T;int n,m;int num;int kase;string st;bool flag;vector<string>prnt;struct masks{ int x,y;}mask[3000];//标记点按照从上往下从左往右排序bool cmp(masks a,masks b){ return a.x<b.x||(a.x==b.x&&a.y<b.y);}//按照字典序排序bool cmp1(string s1,string s2){ int x=0,y=0; while(s1[x]=='.')x++; while(s2[y]=='.')y++; while(x<s1.length()&&y<s2.length()){ if(s1[x]==s2[y]){ x++;y++; } else return s1[x]<s2[y]; }}//初始化void init(){ for(int i=0;i<4;i++){ str[i]=""; ans[i]=""; }}//标记点顺时针旋转90void rot(){ for(int i=0;i<num;i++){ int tmp=mask[i].x; mask[i].x=mask[i].y; mask[i].y=n-tmp-1; } sort(mask,mask+num,cmp);}//读取void read(){ cin>>n; for(int i=0;i<n;i++){ scanf("%s",s[i]); getchar();//必须getchar()吃回车 } num=0; for(int i=0;i<n;i++){ for(int j=0;j<n;j++){ if(getchar()=='*'){ mask[num].x=i; mask[num++].y=j; } } getchar(); } cin>>m; word.clear(); for(int i=0;i<m;i++){ cin>>st; word[st]=1; }}int main(){ cin>>T; kase=0; while(T--){ read(); init(); for(int i=0;i<4;i++){ for(int j=0;j<num;j++){ str[i]+=s[mask[j].x][mask[j].y]; } rot(); } for(int i=0;i<4;i++){ for(int j=0;j<4;j++){ ans[i]+=str[(i+j)%4]; } } sort(ans,ans+4,cmp1); int i; for(i=0;i<4;i++){ flag=true; prnt.clear(); int j=0; while(j<ans[i].length()){ while(j<ans[i].length()&&ans[i][j]=='.')j++; if(j>=ans[i].length())break; st=""; while(j<ans[i].length()&&ans[i][j]!='.') st+=ans[i][j],j++; if(word[st]==0){ flag=false; break; } else { prnt.push_back(st); } } if(flag)break; } cout<<"Case #"<<++kase<<":"; if(i<4){ for(int j=0;j<prnt.size();j++){ cout<<" "<<prnt[j]; } cout<<endl; } else { cout<<" FAIL TO DECRYPT"<<endl; } } return 0;} 阅读全文
0 0
- hdu
- hdu
- HDU
- hdu ()
- hdu
- hdu
- HDU
- HDU
- hdu
- hdu
- HDU
- Hdu
- hdu
- hdu-
- hdu
- hdu
- hdu
- HDU
- 【API】Unity5.6 Animation transitions
- G
- POJ 1222 EXTENDED LIGHTS OUT(高斯消元)
- L1-042. 日期格式化
- tensorflow 全连接神经网络 MNIST手写体数字识别
- HDU
- L1-043. 阅览室
- (0059)iOS开发之添加自定义字体库并设置文本字体
- C++标准泛型算法库的函数为什么设计成不能改变容器大小?
- redux 学习笔记
- MySQL的btree索引和hash索引的区别
- 【HDU
- 上传jar到私服的两种方式From POM和GAV Parameters。使用Nexus管理Maven仓库时,上传带依赖的第三方jar.
- 计算机导论-符号化,计算化与自动化


