How to make transparent bridge with Slackware Linux.
来源:互联网 发布:及时雨淘宝客软件骗局 编辑:程序博客网 时间:2024/05/16 10:43
What is a transparent bridge and why to use it?
Few lines of dry theory first:
- Transparent bridges are used for various tests and security applications.
- Sniffing traffic. (I did this a lot when I worked as QA)
- Delaying traffic and adding loss for testing purposes.
- Logging part of the traffic, without the user notice.
- Firewalling packets, not intended for your network without additional routing.
- Other, we don’t want/need explained (as shaping your GF PC, because she uses too much BW for music while you play MMORPG, or simply spying on her chat logs.)
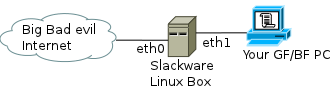
Simple bridge
Basically, we need a Slackware (or any other) Linux box with 2 NICs (network interface cards). In this scenario, we will make a transparent bridge suitable for sniffing traffic and introduce you to some software for this needs. The PC behind the Slackware box should be set with the TCP/IP settings to access the Internet. The bridge we set in front of this PC will be absolutely transparent for any packets passing between the PC and your service provider switch. Have a check if you have the following commands: tc,brctl, tcpdump:
bash-4.1# which tcpdump/usr/sbin/tcpdumpbash-4.1# which tc/sbin/tcbash-4.1# which brctl/sbin/brctlbash-4.1#
The packages we need for this are coming with your distribution and no additional software is needed. Those packages are probably already installed. However, if you made minimal install or did not put category Network, now is the time:
wget ftp://ftp.slackware.com/pub/slackware/slackware-current/slackware/n/bridge-utils-1.4-i486-1.txzwget ftp://ftp.slackware.com/pub/slackware/slackware-current/slackware/n/tcpdump-4.1.1-i486-1.txzwget ftp://ftp.slackware.com/pub/slackware/slackware-current/slackware/n/iproute2-2.6.37-i486-1.txzinstallpkg bridge-utils-1.4-i486-1.txzinstallpkg tcpdump-4.1.1-i486-1.txzinstallpkg iproute2-2.6.37-i486-1.txz
What’s left to do is to enable the linux box to bridge the connection between the Internet and our PC:
bash-4.1# brctl addbr br01bash-4.1# brctl addif br01 eth0bash-4.1# brctl addif br01 eth1bash-4.1# ifconfig br01 upbash-4.1# brctl showbridge namebridge idSTP enabledinterfacesbr018000.00064f295019noeth0eth1bash-4.1# ifconfig br01br01 Link encap:Ethernet HWaddr 00:06:4F:29:50:19 inet6 addr: fe80::206:4fff:fe29:5019/64 Scope:Link UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1 RX packets:0 errors:0 dropped:0 overruns:0 frame:0 TX packets:6 errors:0 dropped:0 overruns:0 carrier:0 collisions:0 txqueuelen:0 RX bytes:0 (0.0 b) TX bytes:468 (468.0 b)bash-4.1#
The bridge is actually up and running after 10 to 15 seconds depending on how fast your Linux box is and what kernel you use. If your ISP is filtering your MAC address in his database, change yours according to the one of your PC’s network card:
bash-4.1# ifconfig br01 hw ether 00:11:22:33:44:55bash-4.1# ifconfig br01br01 Link encap:Ethernet HWaddr 00:11:22:33:44:55 inet6 addr: fe80::206:4fff:fe29:5019/64 Scope:Link UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1 RX packets:0 errors:0 dropped:0 overruns:0 frame:0 TX packets:6 errors:0 dropped:0 overruns:0 carrier:0 collisions:0 txqueuelen:0 RX bytes:0 (0.0 b) TX bytes:468 (468.0 b)bash-4.1#
In this case, you need to rewrite your PC’s MAC address with something else (even random one). Because there will be duplicate MAC address and your Linux box will complain about it. With this set, your home PC will have bridged connection to the ISP with one transparent linux box in between.
The sniffing itself, can be done in 2 ways. With tcpdump and with Wireshark. The first is quick and elegant, the second is pretty and powerful.
bash-4.1# tcpdump -c 100 -i br01 -w dumpfile.pcaptcpdump: WARNING: br01: no IPv4 address assignedtcpdump: listening on br01, link-type EN10MB (Ethernet), capture size 65535 bytes100 packets captured100 packets received by filter0 packets dropped by kernelbash-4.1#
The above explained, -c 100 means get 100 packets (c=count), -i br01 does not need explaining and -w writes at a specific dump file. More for the .pcap extension, below.
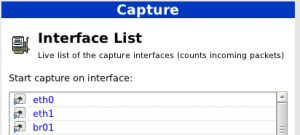
Capture interfaces
If we want the same done with Wireshark, we need to have some Xorg installed and some neat window manager as xfce4 (my own preference since KDE 4.x become one hell of a process spawning Hydra too big for a pentium 4 single core with some cheap video card). You may get this powerful software from its website. The best part in Wireshark is compatibility with tcpdump files captured with console. They are both based on the library libpcap and don’t need much transformation of the data they operate with.
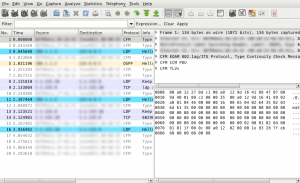
Captured file
So if you need more depth in the packet analysis, get Wireshark and learn how to use it. If the Linux box has console only (You may prefer it that way), use tcpdump to capture traffic and analyze it in Wireshark. The only minus is, Wireshark is more useful on the bridge, much more interactive and can create an ACL list for you directly from the captured traffic. If you want specific address, that’s bugging you filtered – go to the ACL menu and generate iptables rule with 2 clicks and just apply it. It works like a charm.
Now, if we want to delay the traffic a bit, we need to set some additional rules for traffic control. In a nut shell:
bash-4.1# ping 10.3.71.17PING 10.3.71.17 (10.3.71.17) 56(84) bytes of data.64 bytes from 10.3.71.17: icmp_req=1 ttl=128 time=0.128 ms64 bytes from 10.3.71.17: icmp_req=2 ttl=128 time=0.130 ms64 bytes from 10.3.71.17: icmp_req=3 ttl=128 time=0.126 ms64 bytes from 10.3.71.17: icmp_req=4 ttl=128 time=0.131 ms^C--- 10.3.71.17 ping statistics ---4 packets transmitted, 4 received, 0% packet loss, time 2999msrtt min/avg/max/mdev = 0.126/0.128/0.131/0.014 msbash-4.1# tc qdisc add dev eth0 root netem delay 1s bash-4.1# ping 10.3.71.17PING 10.3.71.17 (10.3.71.17) 56(84) bytes of data.64 bytes from 10.3.71.17: icmp_req=1 ttl=128 time=1000 ms64 bytes from 10.3.71.17: icmp_req=2 ttl=128 time=1000 ms64 bytes from 10.3.71.17: icmp_req=3 ttl=128 time=1000 ms64 bytes from 10.3.71.17: icmp_req=4 ttl=128 time=1000 ms^C--- 10.3.71.17 ping statistics ---5 packets transmitted, 4 received, 20% packet loss, time 3999msrtt min/avg/max/mdev = 1000.130/1000.135/1000.149/1.000 ms, pipe 2bash-4.1#
Lots of other stuff can be done with this bridge and Netem (network emulator) but it is far beyond this simple guide.
For further reading.
- How to make transparent bridge with Slackware Linux.
- how to make a transparent histogram in matlab
- How to install Slackware
- How to Install ATI Catalyst on Slackware Linux
- How to configure transparent bridge between SCCP and SIP VoIP systems.
- How to make sexy buttons with CSS
- How to Make cURL works with cmake
- How To Drawing Transparent Bitmaps
- 设置navigation完全透明效果(How to make navigation bar transparent in iOS 7)
- Make background of UITableView to transparent
- How to make linux boot from network
- How to make patch for linux
- how to make one bootable USB stick with OpenSolaris 2008.05
- How to Make Money Online with eBay, Yahoo!, and Google
- How To Make A Simple iPhone Game with Cocos2D Tutorial
- How To Make a Tile Based Game with Cocos2D
- How To Make A Simple iPhone Game with Cocos2D Tutorial
- How to Make a AutoBuild System with Git Server
- linux特殊符号大全
- Linux 进程间通信--- 信号量
- Eclipse+ADT进行Android应用程序的代码混淆和签名
- android 如何预置APK
- 在Linux下,用OpenJTAG+OpenOCD烧写NAND Flash
- How to make transparent bridge with Slackware Linux.
- 详细记录python的range()函数用法
- Linux中断(interrupt)子系统之一:中断系统基本原理
- Java Struts2 实现数据库数据导出Excel文件
- 黑马程序员-params
- NHibernate的插入、删除、修改操作
- windows phone:资源(一)
- 我的SEO之路2013年3月5日最早的一个站突破
- 数据库中状态表的设计


