Howto: Make Your Own Cert With OpenSSL
来源:互联网 发布:南洋华人 知乎 编辑:程序博客网 时间:2024/06/05 09:58
http://blog.didierstevens.com/2008/12/30/howto-make-your-own-cert-with-openssl/
First we generate a 4096-bit long RSA key for our root CA and store it in file ca.key:
openssl genrsa -out ca.key 4096
Generating RSA private key, 4096 bit long modulus...................................................................................++........................................................................++e is 65537 (0x10001)
If you want to password-protect this key, add option -des3.
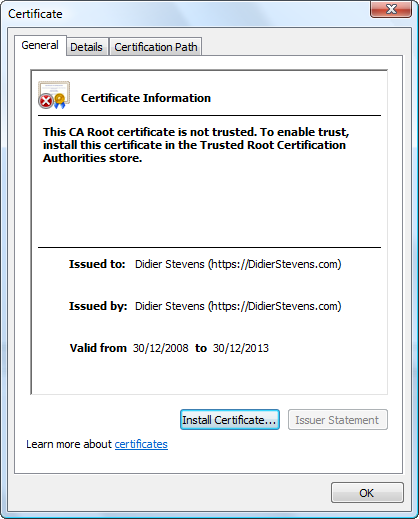
Next, we create our self-signed root CA certificate ca.crt; you’ll need to provide an identity for your root CA:
openssl req -new -x509 -days 1826 -key ca.key -out ca.crt
You are about to be asked to enter information that will be incorporatedinto your certificate request.What you are about to enter is what is called a Distinguished Name or a DN.There are quite a few fields but you can leave some blankFor some fields there will be a default value,If you enter '.', the field will be left blank.-----Country Name (2 letter code) [GB]:BEState or Province Name (full name) [Berkshire]:BrusselsLocality Name (eg, city) [Newbury]:BrusselsOrganization Name (eg, company) [My Company Ltd]:https://DidierStevens.comOrganizational Unit Name (eg, section) []:Common Name (eg, your name or your server's hostname) []:Didier Stevens (https://DidierStevens.com)Email Address []:didier stevens Google mail
The -x509 option is used for a self-signed certificate. 1826 days gives us a cert valid for 5 years.
Next step: create our subordinate CA that will be used for the actual signing. First, generate the key:
openssl genrsa -out ia.key 4096
Generating RSA private key, 4096 bit long modulus.....++.............................................................................++e is 65537 (0x10001)
Then, request a certificate for this subordinate CA:
openssl req -new -key ia.key -out ia.csr
You are about to be asked to enter information that will be incorporatedinto your certificate request.What you are about to enter is what is called a Distinguished Name or a DN.There are quite a few fields but you can leave some blankFor some fields there will be a default value,If you enter '.', the field will be left blank.-----Country Name (2 letter code) [GB]:BEState or Province Name (full name) [Berkshire]:BrusselsLocality Name (eg, city) [Newbury]:BrusselsOrganization Name (eg, company) [My Company Ltd]:https://DidierStevens.comOrganizational Unit Name (eg, section) []:Didier Stevens Code Signing (https://DidierStevens.com)Common Name (eg, your name or your server's hostname) []:Email Address []:didier stevens Google mailPlease enter the following 'extra' attributesto be sent with your certificate requestA challenge password []:An optional company name []:
Next step: process the request for the subordinate CA certificate and get it signed by the root CA.
openssl x509 -req -days 730 -in ia.csr -CA ca.crt -CAkey ca.key -set_serial 01 -out ia.crt
Signature oksubject=/C=BE/ST=Brussels/L=Brussels/O=https://DidierStevens.com/OU=Didier Stevens Code Signing (https://DidierStevens.com)/emailAddress=didier stevens Google mailGetting CA Private Key
The cert will be valid for 2 years (730 days) and I decided to choose my own serial number 01 for this cert (-set_serial 01). For the root CA, I let OpenSSL generate a random serial number.
That’s all there is to it! Of course, there are many options I didn’t use. Consult theOpenSSL documentation for more info. For example, I didn’t restrict my subordinate CA key usage to digital signatures. It can be used for anything, even making another subordinate CA. When you buy a code signing certificate, the CA company will limit its use to code signing.

To use this subordinate CA key for Authenticode signatures with Microsoft’s signtool, you’ll have to package the keys and certs in a PKCS12 file:
openssl pkcs12 -export -out ia.p12 -inkey ia.key -in ia.crt -chain -CAfile ca.crt
Enter Export Password:Verifying - Enter Export Password:
To sign executables in Windows with the signtool: install file ia.p12 in your certificate store (e.g. double click it), and then use signtool /wizard to sign your PE file.
I’ve used this process to generate certs for my own code signing, and for my Authenticode Challenge.
- Howto: Make Your Own Cert With OpenSSL
- Make Your Own 2d Games With Construct 2
- make your own phpstorm epa
- MAKE YOUR OWN NEURAL NETWORK
- Make your own kind of music
- Make your own mini Linux OS
- How to make your own VST host
- How to make your own maps/tiles
- Make Your Own Neural Network简介
- Set up your own PBX with Asterisk
- Develop your own filesystem with FUSE
- Build Your Own PaaS with Docker.pdf
- Augmenting IDA UI with your own actions.
- Simple SSL cert - HOWTO
- Sometimes You Can't Make it On Your Own
- Sometimes You Can't Make it On Your Own
- |||Make your own Computer Software - without Programming!_7034
- Make your own Neural NetWork之代码详解上
- 算法导论计数排序实现(C++)
- Spring学习(八)spring整合struts2
- java高级之类反射
- apache下设置缓存方法详细介绍
- iOS Today Extension/widget编程小记
- Howto: Make Your Own Cert With OpenSSL
- 百度最新面试题集锦
- Can I become a good programmer without math and algorithms knowledge?
- Processing 教程(0): Get started!
- SQL Server 2008 R2创建定期自动备份任务
- 2014ACM-ICPC亚洲区域西安赛区 G题 / GYM 100548 G
- System V 信号灯
- JSON 入门
- iwi的模板


