poj1107 解密模拟
来源:互联网 发布:算法及其描述 2 1 编辑:程序博客网 时间:2024/05/16 12:24
W's Cipher
Time Limit: 1000MS Memory Limit: 10000KTotal Submissions: 5429 Accepted: 2718
Description
Weird Wally's Wireless Widgets, Inc. manufactures an eclectic assortment of small, wireless, network capable devices, ranging from dog collars, to pencils, to fishing bobbers. All these devices have very small memories. Encryption algorithms like Rijndael, the candidate for the Advanced Encryption Standard (AES) are demonstrably secure but they don't fit in such a tiny memory. In order to provide some security for transmissions to and from the devices, WWWW uses the following algorithm, which you are to implement.
Encrypting a message requires three integer keys, k1, k2, and k3. The letters [a-i] form one group, [j-r] a second group, and everything else ([s-z] and underscore) the third group. Within each group the letters are rotated left by ki positions in the message. Each group is rotated independently of the other two. Decrypting the message means doing a right rotation by ki positions within each group.
Consider the message the_quick_brown_fox encrypted with ki values of 2, 3 and 1. The encrypted string is _icuo_bfnwhoq_kxert. The figure below shows the decrypting right rotations for one character in each of the three character groups.
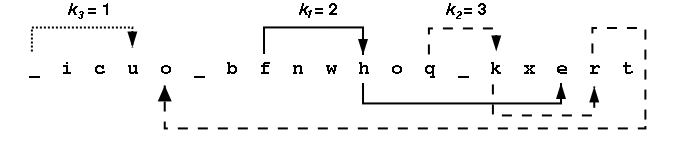
Looking at all the letters in the group [a-i] we see {i,c,b,f,h,e} appear at positions {2,3,7,8,11,17} within the encrypted message. After a right rotation of k1=2, these positions contain the letters {h,e,i,c,b,f}. The table below shows the intermediate strings that come from doing all the rotations in the first group, then all rotations in the second group, then all the rotations in the third group. Rotating letters in one group will not change any letters in any of the other groups.
All input strings contain only lowercase letters and underscores(_). Each string will be at most 80 characters long. The ki are all positive integers in the range 1-100.
Encrypting a message requires three integer keys, k1, k2, and k3. The letters [a-i] form one group, [j-r] a second group, and everything else ([s-z] and underscore) the third group. Within each group the letters are rotated left by ki positions in the message. Each group is rotated independently of the other two. Decrypting the message means doing a right rotation by ki positions within each group.
Consider the message the_quick_brown_fox encrypted with ki values of 2, 3 and 1. The encrypted string is _icuo_bfnwhoq_kxert. The figure below shows the decrypting right rotations for one character in each of the three character groups.
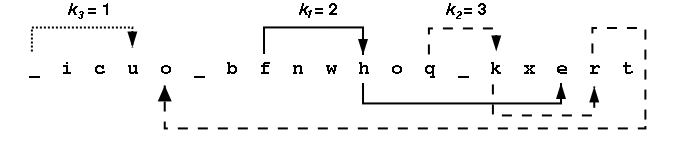
Looking at all the letters in the group [a-i] we see {i,c,b,f,h,e} appear at positions {2,3,7,8,11,17} within the encrypted message. After a right rotation of k1=2, these positions contain the letters {h,e,i,c,b,f}. The table below shows the intermediate strings that come from doing all the rotations in the first group, then all rotations in the second group, then all the rotations in the third group. Rotating letters in one group will not change any letters in any of the other groups.
All input strings contain only lowercase letters and underscores(_). Each string will be at most 80 characters long. The ki are all positive integers in the range 1-100.
Input
Input consists of information for one or more encrypted messages. Each problem begins with one line containing k1, k2, and k3 followed by a line containing the encrypted message. The end of the input is signalled by a line with all key values of 0.
Output
For each encrypted message, the output is a single line containing the decrypted string.
Sample Input
2 3 1_icuo_bfnwhoq_kxert1 1 1bcalmkyzx3 7 4wcb_mxfep_dorul_eov_qtkrhe_ozany_dgtoh_u_eji2 4 3cjvdksaltbmu0 0 0
Sample Output
the_quick_brown_foxabcklmxyzthe_quick_brown_fox_jumped_over_the_lazy_dogajsbktcludmv
题意:把小写字母分为三组,第一组是 a~i 第二组 j~r 第三组是s~z 和 _
然后每一组分别按照 k1 k2 k3 的方式旋转每一组字符串
举个栗子:若一组是 i,c,b,f,h,e 对应的 k值为 2,则旋转后就变成 h e i,c,b,f
需要注意的地方是:
k 值可能比对应的一组的字符长度还要长,所以需要取模,取模的时候需要注意是不是 负数
代码如下:
#include<stdio.h>#include<string.h>#include<math.h>#include<algorithm>using namespace std;typedef struct G{ char letter; int pos;}t;t group[5][100];char a[100];int main(){ int k[5]; while(scanf("%d%d%d",&k[1],&k[2],&k[3]),k[1]+k[2]+k[3]!=0) { scanf("%s",a); int len=strlen(a); int pos[5]; pos[1]=0;pos[2]=0;pos[3]=0; for(int i=0;i<len;i++){ char temp=a[i]; if(temp>='a'&&temp<='i'){ group[1][pos[1]].letter=temp; group[1][pos[1]++].pos=i; } else if(temp>='j'&&temp<='r'){ group[2][pos[2]].letter=temp; group[2][pos[2]++].pos=i; } else{ group[3][pos[3]].letter=temp; group[3][pos[3]++].pos=i; } } for(int i=1;i<=3;i++){ char temp_str[100]; int p=0; int q; for(int j=abs(pos[i]*200-k[i]),q=0;q<pos[i];j++,q++) temp_str[p++]=group[i][j%pos[i]].letter; for(int j=0;j<pos[i];j++) a[group[i][j].pos]=temp_str[j]; } for(int i=0;i<len;i++) printf("%c",a[i]); puts(""); } return 0;} 0 0
- poj1107 解密模拟
- poj1107
- POJ1107
- POJ1107 W's Cipher 简单模拟
- POJ1107 W's Cipher
- 解密模拟题
- GDOI2016模拟8.18解密
- POJ1107 W's Cipher 【水题】
- [GDOI模拟2015.08.18]解密
- poj1107 W's Cipher(字符串)
- 模拟文件的加密与解密
- HardLock 加密狗模拟解密硬复制HardLock
- HASP 4 加密狗模拟、解密硬复制HASP 4
- Hasp HL加密狗模拟、解密硬复制Hasp HL
- ZOJ 1006 Do the Untwist 加密解密 模拟
- POJ 1107 W's Cipher (模拟解密)
- 解密jQuery事件核心 - 模拟事件(四)
- bestcoder 1002 列变位法解密(模拟)
- PreferenceActivity使用详解
- HDU 5605 geometry
- java Socket实现简单在线聊天(一)
- mysql 分页
- Unable to find explicit activity class
- poj1107 解密模拟
- HZAUoj 1016: Array C 【贪心】
- java Socket实现简单在线聊天(二)
- 模仿微信选择群组成员的搜索效果(退格删除成员)
- 访问其他机器的资料
- Linux查看物理CPU个数、核数、逻辑CPU个数
- 用类的成员函数,定义复数类重载运算符+、-、*、/,使之能用于复数的加减乘除
- java Socket实现简单在线聊天(三)
- Shell算术运算


