poj 2635 The Embarrassed Cryptographer(同余模定理的应用)
来源:互联网 发布:如何在淘宝打开链接 编辑:程序博客网 时间:2024/06/05 05:53
题目链接:点击打开链接
Description
 The young and very promising cryptographer Odd Even has implemented the security module of a large system with thousands of users, which is now in use in his company. The cryptographic keys are created from the product of two primes, and are believed to be secure because there is no known method for factoring such a product effectively.
The young and very promising cryptographer Odd Even has implemented the security module of a large system with thousands of users, which is now in use in his company. The cryptographic keys are created from the product of two primes, and are believed to be secure because there is no known method for factoring such a product effectively. What Odd Even did not think of, was that both factors in a key should be large, not just their product. It is now possible that some of the users of the system have weak keys. In a desperate attempt not to be fired, Odd Even secretly goes through all the users keys, to check if they are strong enough. He uses his very poweful Atari, and is especially careful when checking his boss' key.
Input
The input consists of no more than 20 test cases. Each test case is a line with the integers 4 <= K <= 10100 and 2 <= L <= 106. K is the key itself, a product of two primes. L is the wanted minimum size of the factors in the key. The input set is terminated by a case where K = 0 and L = 0.
Output
For each number K, if one of its factors are strictly less than the required L, your program should output "BAD p", where p is the smallest factor in K. Otherwise, it should output "GOOD". Cases should be separated by a line-break.
Sample Input
143 10143 20667 20667 302573 302573 400 0Sample Output
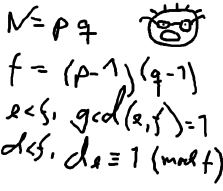
GOODBAD 11GOODBAD 23GOODBAD 31基本思路:用到同于模定理的知识,我也是现学的,接触到了个新知识点,可以访问同余模定理文库学习相关知识.然后在再优化,将10进制的转化为1000进制的,避免在循环时超时,具体怎么做上面那个链接很清楚.
<span style="font-size:18px;">#include <iostream>#include<cstring>#include<cstdio>#include<cstdlib>using namespace std;char s[1000];int prime[1000100];int top;bool vis[1000100];int big[1000];///筛选素数void chooseprime(){ memset(vis,0,sizeof(vis)); for(int i=2;i<=1000015;i++) { if(!vis[i]) { prime[++top]=i; for(int j=i+i;j<=1000015;j=j+i) { if(j%i==0)vis[j]=1; } } }}int main(){ chooseprime(); int n; while(scanf("%s%d",s,&n)) { if(n==0&&s[0]=='0')break; int sum=0,ans=0; int len=strlen(s); int t; int k=0; ///转化为1000进制,注意从个位开始 for(int i=len-1;i>=0;i--) { t=s[i]-'0'; for(int j=1;j<=ans;j++) t=t*10; sum=sum+t; ans++; if(ans==3) { big[++k]=sum; sum=ans=0; } } if(sum!=0)big[++k]=sum; int f=0; int ant; ///查找素数 for(int i=1;i<=top;i++) { int m=prime[i]; if(m>=n)break;///因为是从小到大寻找素数,如果小的不符合,那么 ///后面的素数一定不符合 int d=0; for(int j=k;j>=1;j--)///从最高位进行同余模定理的应用 { d=(d*1000+big[j])%m; } if(d==0) { f=1; ant=m; break; } } if(f) { cout<<"BAD "<<ant<<endl; } else cout<<"GOOD\n"; } return 0;}</span> 1 0
- poj 2635 The Embarrassed Cryptographer(同余模定理的应用)
- The Embarrassed Cryptographer POJ 2635 数论之高精度求模(同余模定理+千进制)
- POJ 2635 The Embarrassed Cryptographer(高精度取模 + 同余模定理)
- poj 2635 The Embarrassed Cryptographer(同余模运算)
- POJ 2635 The Embarrassed Cryptographer [高精度求余+同余模定理]【数论】
- POJ 2635-The Embarrassed Cryptographer(高精度求模+同余模定理)
- POJ 2635 The Embarrassed Cryptographer【数论,千进制,高精度求模+同余模定理】
- poj 2635 The Embarrassed Cryptographer(素数筛 + 同余模定理)
- [ACM] POJ 2635 The Embarrassed Cryptographer (同余定理,素数打表)
- poj 2635 The Embarrassed Cryptographer (同余定理,筛选法)
- poj The Embarrassed Cryptographer(大数取模)(同余模定理)
- POJ 2635 The Embarrassed Cryptographer (同余线性方程+素数筛)
- POJ 2635 The Embarrassed Cryptographer (同余问题)
- POJ2635 The Embarrassed Cryptographer (同余)
- POJ 2635 The Embarrassed Cryptographer(素数筛+高精度求模+同余模)
- (POJ2635)The Embarrassed Cryptographer <高精度求模(千进制表示) + 同余模定理 + 素数打表>
- poj 2635 The Embarrassed Cryptographer(同余模取余+万进制)
- POJ 2635 The Embarrassed Cryptographer
- Arp攻击实战
- 简版服务器(c语言实现)
- POJ-1383-Labyrinth(广搜最大直径)
- 关于mysql绿色版安装遇到问题的处理
- 二叉树的序列化和反序列化
- poj 2635 The Embarrassed Cryptographer(同余模定理的应用)
- 如何自我营销
- hdoj-【最短路】
- 算法之------深度优先搜索DFS和广度优先搜索BFS(最短路径)
- 组合自定义控件
- NYOJ 586.疯牛(二分枚举+贪心)
- Web入侵攻击方式
- Redis数据备份与恢复
- 判断链表是否有环的两种方式和创建有无环的方法


