160个CrackMe 028 Cosh.2
来源:互联网 发布:淘宝一件代发供货平台 编辑:程序博客网 时间:2024/06/06 09:49
首先PEID查壳: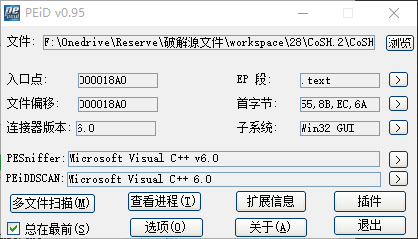
没有壳,位码验证: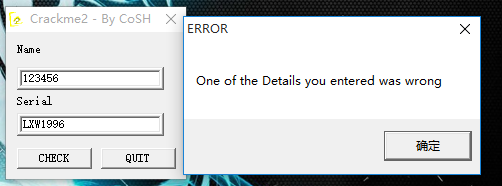
发现了错误字符串,于是OD中查找参考文本字符串进行跟进: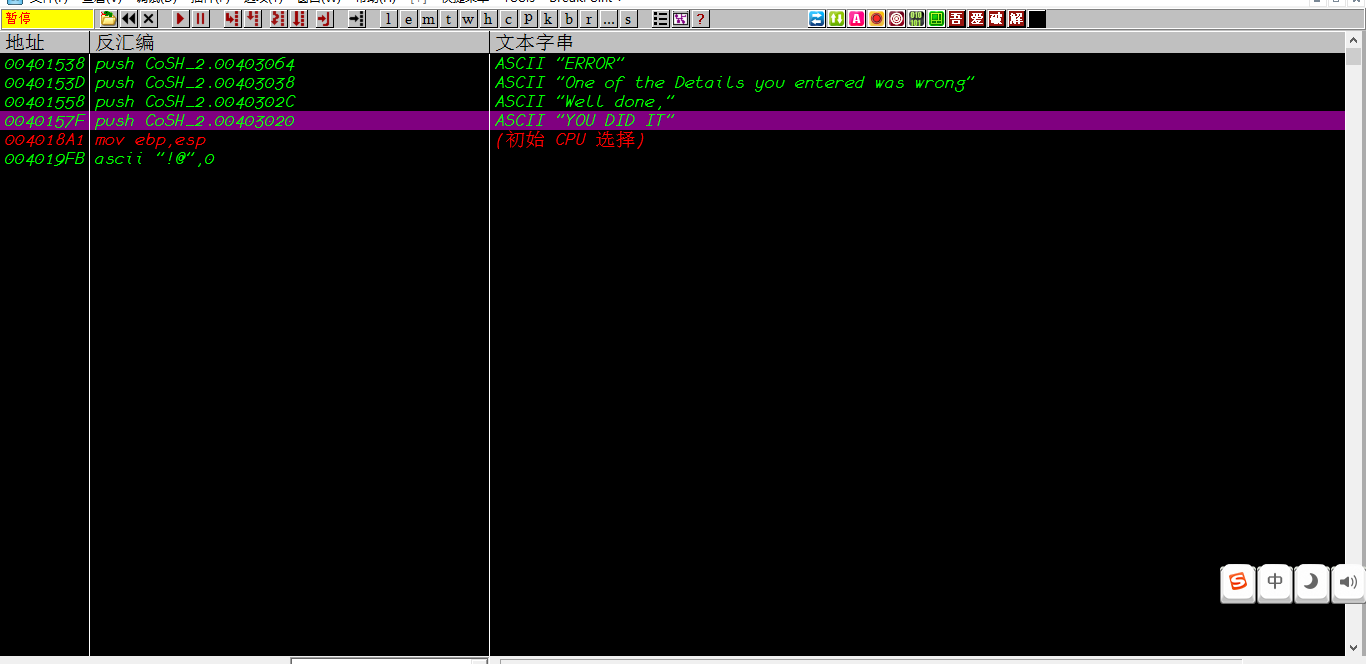
在OD中找到相应的分支结构:
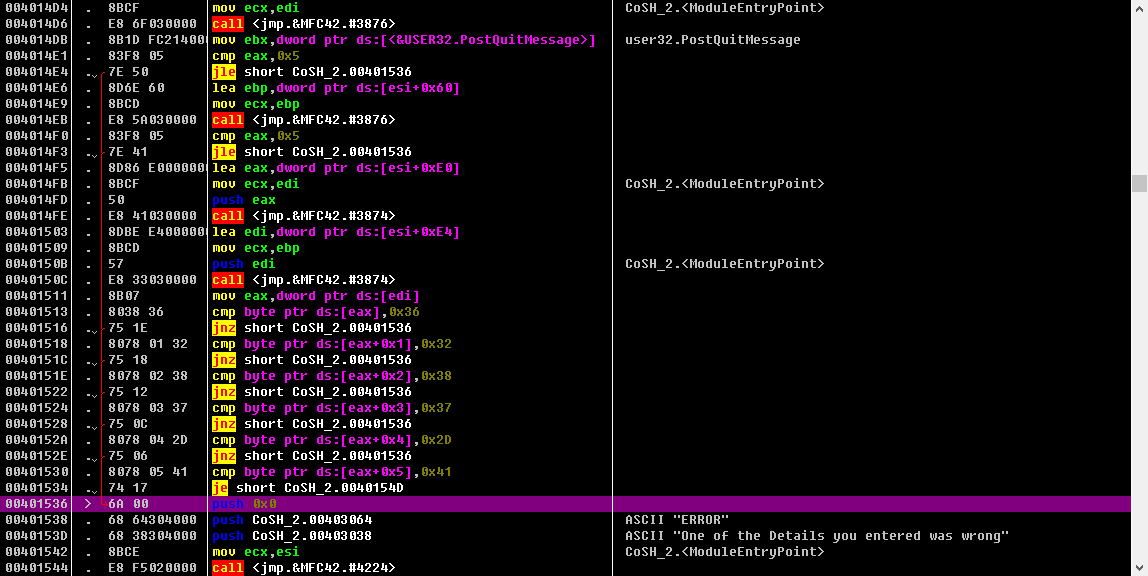
在上面的函数头部下断点,单步键入,分析代码:简单,略过,最后发现实际没有算法,就是serial硬编码,把十六进制转换成ASCII码即可。
004014CA . 56 push esi004014CB . 8BF1 mov esi,ecx004014CD . 57 push edi004014CE . 8DBE A0000000 lea edi,dword ptr ds:[esi+0xA0]004014D4 . 8BCF mov ecx,edi004014D6 . E8 6F030000 call <jmp.&MFC42.#3876>004014DB . 8B1D FC214000 mov ebx,dword ptr ds:[<&USER32.PostQuitMessage>] ; user32.PostQuitMessage004014E1 . 83F8 05 cmp eax,0x5 ; ;获取name字符串的长度,判断是否大于5004014E4 . 7E 50 jle short CoSH_2.00401536 ; ;字符串长度小于等于5,错误004014E6 . 8D6E 60 lea ebp,dword ptr ds:[esi+0x60]004014E9 . 8BCD mov ecx,ebp004014EB . E8 5A030000 call <jmp.&MFC42.#3876> ; ;获取serial字符串的长度004014F0 . 83F8 05 cmp eax,0x5 ; ;判断是否大于5004014F3 . 7E 41 jle short CoSH_2.00401536 ; ;字符串长度小于等于5,错误004014F5 . 8D86 E0000000 lea eax,dword ptr ds:[esi+0xE0]004014FB . 8BCF mov ecx,edi004014FD . 50 push eax004014FE . E8 41030000 call <jmp.&MFC42.#3874>00401503 . 8DBE E4000000 lea edi,dword ptr ds:[esi+0xE4]00401509 . 8BCD mov ecx,ebp0040150B . 57 push edi0040150C . E8 33030000 call <jmp.&MFC42.#3874>00401511 . 8B07 mov eax,dword ptr ds:[edi]00401513 . 8038 36 cmp byte ptr ds:[eax],0x36 ; ;serila的第一个与0x36比较00401516 . 75 1E jnz short CoSH_2.0040153600401518 . 8078 01 32 cmp byte ptr ds:[eax+0x1],0x32 ; ;serila的第二个字符与0x32比较0040151C . 75 18 jnz short CoSH_2.004015360040151E . 8078 02 38 cmp byte ptr ds:[eax+0x2],0x38 ; ;serila的第三个字符与0x38比较00401522 . 75 12 jnz short CoSH_2.0040153600401524 . 8078 03 37 cmp byte ptr ds:[eax+0x3],0x37 ; ;serila的第四个字符与0x37比较00401528 . 75 0C jnz short CoSH_2.004015360040152A . 8078 04 2D cmp byte ptr ds:[eax+0x4],0x2D ; ;serila的第五个字符与0x2D比较0040152E . 75 06 jnz short CoSH_2.0040153600401530 . 8078 05 41 cmp byte ptr ds:[eax+0x5],0x41 ; ;serila的第六个字符与0x41比较00401534 . 74 17 je short CoSH_2.0040154D00401536 > 6A 00 push 0x000401538 . 68 64304000 push CoSH_2.00403064 ; ASCII "ERROR"0040153D . 68 38304000 push CoSH_2.00403038 ; ASCII "One of the Details you entered was wrong"00401542 . 8BCE mov ecx,esi00401544 . E8 F5020000 call <jmp.&MFC42.#4224>00401549 . 6A 00 push 0x00040154B . FFD3 call ebx ; user32.PostQuitMessage0040154D > 8D8E E0000000 lea ecx,dword ptr ds:[esi+0xE0]00401553 . 8D5424 14 lea edx,dword ptr ss:[esp+0x14]00401557 . 51 push ecx00401558 . 68 2C304000 push CoSH_2.0040302C ; ASCII "Well done,"0040155D . 52 push edx0040155E . E8 D5020000 call <jmp.&MFC42.#926>检验一下serial:
6287-A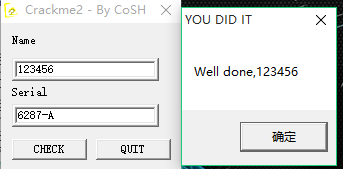
最后,根据程序的流程写注册机
C++:
#include <iostream>#include <cstring>using namespace std;#define N 100int main(){ char name[N]; char serial_true[N]={0x36,0x32,0x38,0x37,0x2D,0x41}; char serial_false[N]; cout<<"Please input your name:"<<endl; cin>>name; cout<<"Please input your serial:"<<endl; cin>>serial_false; if(strlen(name)<=5||strlen(serial_false)<=5) { cout<<"Error!"<<endl; return 0; } else { cout<<"True serial is only behind the string:"<<endl; for(int i=0;i<=6;i++) { cout<<serial_true[i]; } cout<<endl; } return 0;}运行结果: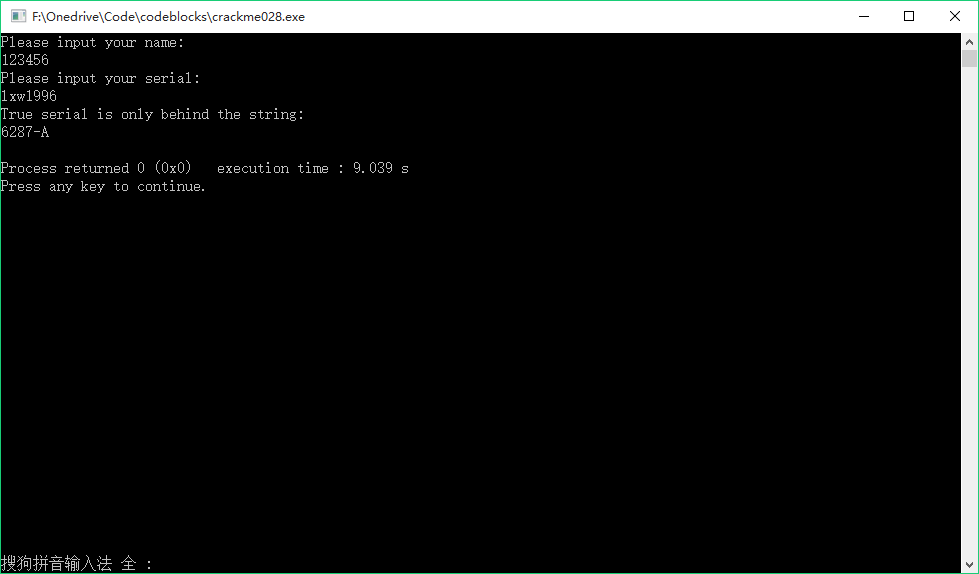
真是水题..
0 0
- 160个CrackMe 028 Cosh.2
- 160个CrackMe 027 Cosh.1
- 160个CrackMe 029 Cosh.3
- 160个练手CrackMe-028
- 160个CrackMe 003 Afkayas.2
- 160个CrackMe-第九个
- CRACKME-160-第79个
- 160个CrackMe-1-Acid_burn
- 160个CrackMe 077 firework2
- 160个CrackMe之001
- 160个crackme之003
- 160个crackme之004
- 160个crackme之008
- 160个crackme之009
- 160个crackme之010
- 160个crackme之011
- 160个CrackMe之11
- 160个CrackMe之91
- 关于C语言字符串和指针的总结
- 二、CSS笔记
- jquery :visible Selector 用于判断元素是否显示
- 自定义Dialog 中setView方法多次调用出错
- 160个CrackMe 027 Cosh.1
- 160个CrackMe 028 Cosh.2
- 160个CrackMe 029 Cosh.3
- Android无需权限显示悬浮窗, 兼谈逆向分析app
- Android Studio常用快捷键、Android Studio快捷键大全
- 笔记-Android Studio配置OpenCV
- iOS-NSURLCache
- windows 8.1 64位PC,Visual Studio 2013 Ultimate,C# .NET 4.0,环境下编写windows服务,亲测成功!
- 一些jquery技巧
- 对存储多路径的测试


